Proposes GAO Investigation of CIA’s Section 702-Like Program As Congress debates reform of Section 702, Patrick Eddington, former CIA analyst turned Cato Institute senior fellow, offers a timely reminder of how much we don’t know about government surveillance of Americans.
In a piece in The Orange County Register, Eddington writes that for years prior to the 9/11 attacks, the CIA was “apparently conducting exactly the kind of internet ‘backbone’ surveillance now carried out under FISA Section 702 … with absolutely no judicial oversight.” Eddington notes that it took a lawsuit under the Freedom of Information Act against the Privacy and Civil Liberties Oversight Board (PCLOB) to reveal an audit by the Inspector General of the CIA that covered 1999-2000. The audit is heavily redacted. Despite the fact that millions of Americans live, work, and travel abroad, under the CIA’s Section 702-like program, the agency presumed a target was foreign when starting collection. The CIA only allegedly ended collection when it discovered the target was in fact an American. The CIA IG report admitted it “was unable to review every regulated activity.” Did other CIA collection activities ensnare the communications of Americans? Most important, Eddington writes that the redactions prevent us from knowing if this CIA program was terminated or if it still operating. What can be done? First, Eddington points to Rep. Nancy Mace (R-SC) and Jamie Raskin (D-MD), who last year tasked the Government Accountability Office to investigate the FBI’s use of “assessments” – de facto investigations that can be opened on any person or organization absent any criminal predicate. Eddington proposes Congress instruct GAO to expand its surveillance program inquiry to include the CIA’s surveillance program. A good place for the GAO to start would be to determine if this program is, in fact, still in operation. Second, Congress should look to the solutions of the Government Surveillance Reform Act to curb widespread abuses, including those in FISA’s Section 702, which also targets digital communications passing through the backbone of major telecommunications firms and internet service providers’ networks. The absence of sunlight is sure to provide a breeding ground for many abuses. Last week, we suggested that the last days of November could prove decisive for reform of Section 702 of the Foreign Intelligence Surveillance Act (FISA).
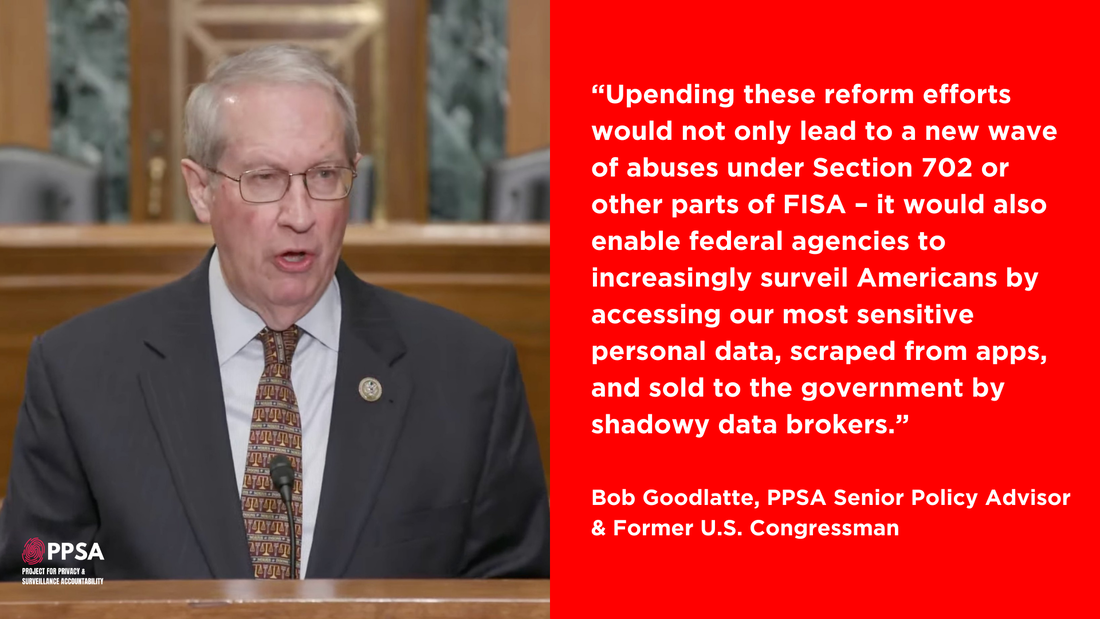
Now word has broken that Congressional leadership is contemplating bypassing Congressional debate by attaching Section 702 to the must-pass National Defense Authorization Act (NDAA), which keeps the military afloat, alight, and on its feet. We are hearing that some wish to attach a version authored by the House Permanent Select Committee on Intelligence (HPSCI), a bill that has at best weak, cosmetic reforms of this authority. Such a move would arm-twist a bicameral, bipartisan majority that wants substantive reforms in Section 702. This majority exists because Section 702 is a program enacted by Congress to surveil foreigners on foreign soil but has been used by the FBI and other agencies as a domestic spying program. In a recent year, Section 702 has been used to warrantlessly capture the communications of 3.4 million Americans. If House and Senate leaders choose this path, it will force Members into an up-or-down vote on a critical bill, with limited debate and no opportunity to make last-minute amendments. In a letter to Congressional Republicans, former House Judiciary Committee Chairman Bob Goodlatte and PPSA Senior Policy Advisor laid out what’s so wrong with HPSCI’s approach:
“There is no reason to rush this process and give the Administration what it wants by sneaking HPSCI’s deeply flawed proposal into the NDAA,” Goodlatte wrote. “In fact, the current Section 702 FISA Court certification does not expire until April 10, 2024, which means Congress has several months to put together a package of real reforms that could justify extending Section 702.” Attaching Section 702 to the NDAA would derail the work of the House Judiciary Committee, which shares jurisdiction over intelligence programs with HPSCI. The House Judiciary Committee is well down the path of drafting a bill. Extending the NDAA would be a sign of significant disrespect for this committee and all the Members, left and right, who have shown a strong interest in debating this program. “Instead of jamming Members and daring them to oppose the NDAA, Leadership should proceed through regular order and let the House Judiciary Committee lead the way with its bipartisan surveillance reform efforts, drawing inspiration from the Government Surveillance Reform Act of 2023,” Goodlatte wrote. “This issue is far too important to turn it into a game of political chicken in the NDAA.” A recent opinion-editorial in The Hill casts a harsh light on the unfolding state of “digital authoritarianism” in America’s schools. Public schools are increasingly adopting artificial intelligence to monitor students and shape curricula. This trend could ultimately have the effect of stifling education, invading privacy, and changing the attitude of adult American society about pervasive surveillance.
Civil rights attorney Clarence Okoh writes that “controversial, data-driven technologies are showing up in public schools nationwide at alarming rates.” These technologies include AI-enabled systems such as “facial recognition, predictive policing, geolocation tracking, student device monitoring and even aerial drones.” A report compiled by the Center for Democracy & Technology found that over 88 percent of schools use student device monitoring, 33 percent use facial recognition and 38 percent share student data with law enforcement. These surveillance technologies enable schools to punish students with greater frequency. A study conducted by Johns Hopkins University found that students at high schools with prominent security measures have lower math scores, are less likely to attend college, and are suspended more often compared to students in schools with less surveillance. The study claims to factor out social and economic background data. Okoh highlights a Florida case in which the sheriff’s office has purportedly used a secret predictive policing program against vulnerable schoolchildren. At some point, the punishments of “predictive” behavior could easily become a self-fulfilling prophecy. A group known as the People Against the Surveillance of Children and Overpolicing (PASCO) has found through litigation and open records requests that the Pasco, Florida, sheriff’s office has a secret youth database that contains the names of up to 18,000 children each academic year. According to PASCO, the sheriff’s office built this database using an algorithm that assessed confidential student records: everything from grades, attendance records, and histories of child abuse are used to assess a student’s risk of falling into “a life of crime.” Many programs directly target minority students. Wisconsin uses a dropout prevention algorithm that uses race as a risk factor. Such modeling, mixed with surveillance software in schools, could have a demonstrably harsher impact on minority students, leading to higher suspension rates. State legislators need to drill down into these reports and verify these claims. One avenue to explore is the role of parents in this process. Are they informed of these practices? Have they been sufficiently heard on them? We have sympathy for why some schools would feel the need to resort to such tactics. But if these facts pan out, then artificial intelligence has just opened up a new front – not just in the war on privacy, but one that could seal the fate of children’s future lives. It also could have an impact on adult society as well. An elementary school student might not understand what it means to be surveilled 24/7 and could become accustomed to it over time. This could lead to a generation of Americans who are inured to ever-present monitoring. If digital authoritarianism becomes the norm in school, it will soon become the norm in society. PPSA looks forward to further developments in this story. When Richard Nixon wanted his minions to run a super-secret surveillance operation that came to be known as the White House Plumbers, the president had it set up in Room 16 in the basement of the Executive Office Building. A recent White House memo obtained and reported by Wired shows that a massive dragnet surveillance program – warrantlessly scooping up phone records from Americans by the trillions – is now being run out of the White House today.
This program, currently called Data Analytical Services (DAS) allows federal, state, and local law enforcement to mine the details, though not the content, of Americans’ calls. As a study at Stanford University showed, metadata alone can reveal startling amounts of highly personal information. When the government adds “chain analysis” – moving outward from one target to the person he or she communicated with, and on to the next person – vast networks of associational groups, whether religious, political, or journalistic, can be X-rayed. “In response to a 2019 Freedom of Information Act request the Project for Privacy and Surveillance Accountability filed jointly with Demand Progress, we received a document from the Drug Enforcement Administration with a redaction into which one could easily fit the word ‘Hemisphere’” said Gene Schaerr, PPSA general counsel. “Hemisphere was the name of this warrantless surveillance program until it was rebranded as Data Analytical Services. Clearly, the government was holding on to something it didn’t want us to see. We had no idea, however, they were hiding it in the White House. With the ‘two-hop’ rule, government at all levels can not only target an individual, but also her spouse, children, parents, and friends. “This is nothing less than warrantless, dragnet surveillance at the national level,” Schaerr said. There is as of yet no evidence that implicates this program in political surveillance. But as with the Nixon Administration, running a program out of the White House has unique advantages. In the current era, a White House operation is not subject to the requirement to review its privacy impacts. It also cannot be subject to FOIA requests. Wired reports that the memo shows that over the years the White House has provided more than $6 million to target the records of any calls that cross AT&T’s infrastructure. Wired also reports that White House funding had intermittent starts and cancellations under the current and last two presidents. Still, the program seems to have been in continuous operation for over a decade. Internal records suggest that the government can access records held by AT&T for at least ten years. These records include the names of callers and recipients, the dates and times of their calls, and their location histories, although the 2018 Supreme Court opinion, Carpenter v. United States, established a warrant requirement for location data. On Sunday, Sen. Ron Wyden (D-OR) fired off a letter to Attorney General Merrick Garland saying, “I have serious concerns about the legality of this surveillance program, and the materials provided by the DOJ contain troubling information that would justifiably outrage many Americans and other Members of Congress.” This breaking news story is certain to provide more momentum for the Government Surveillance Reform Act (GSRA), and the inclusion of a broad warrant requirement and other reforms within a House Judiciary Committee reform bill now being drafted. As this story makes clear, we must have these reforms before any extension of Section 702 of the Foreign Intelligence Surveillance Act can be contemplated. Revival of Notorious ‘Lone Wolf’ Spying on Americans’ Browsing, Biometrics? The intelligence community and its champions on Capitol Hill are frantic, perhaps even panicked, as they see the approach of the end-of-the-year deadline for the reauthorization of Section 702 of the Foreign Intelligence Surveillance Act. The result is a furious throw-spaghetti-at-the-wall strategy in a vain effort to get something to stick – as long as it doesn’t look like reform.
At the heart of this controversy is whether this authority – enacted by Congress to enable the surveillance of foreigners on foreign soil – should require a probable cause warrant, as mandated by Fourth Amendment, when the government examines Americans’ personal communications collected under Section 702. The White House declared that a warrant for such U.S. person queries would constitute a “red line.” It is not clear, however, if President Biden would actually follow through on his threat to veto the reauthorization of Section 702. FBI Director Christopher Wray in prepared remarks said that having a warrant requirement would entail “profound risks,” forcing the expenditure of “scarce resources, the submission and review of a lengthy legal filing, and the passage of significant time – which, in the world of rapidly evolving threats, the government does not always have.” He is contradicted by David Aaron, former senior attorney for the Department of Justice National Security Division. Aaron wrote that a warrant requirement would be “a relatively light burden on the government.” Beyond rhetoric, the champions of the intelligence community in Congress last Sunday tried to attach a “clean” – that is, an unchanged extension of Section 702 without reforms – into the budgetary continuing resolution. This resulted in an immediate response from leading champions of civil liberties and a determined pushback from almost thirty civil liberties organizations from left, right, and center. When that failed, the opponents of reform pivoted and proposed attaching their extension of Section 702 in the must-pass National Defense Authorization Act (NDAA). PPSA’s Senior Policy Advisors Bob Goodlatte, former Chairman of the House Judiciary Committee, and Mark Udall, who served on the Senate Select Committee on Intelligence, dispatched a letter to Members warning against this legislative legerdemain. The threat of such an extension of Section 702 in the NDAA seems to have now receded. Also last week, the House Permanent Select Committee on Intelligence released a bill disingenuously labeled a reform bill. It contains a warrant requirement limited to a narrow subset of “evidence of a crime” surveillance queries, while allowing the FBI to continue to define pretty much anything else as a matter of national security worthy of warrantless surveillance. This leaves unclear how the FBI would meet the bill’s evidence-of-a-crime warrant standard but not a broader warrant requirement. This measure appears to be intentionally designed to be either taken out of the bill or simply ignored by the FBI in practice. As Sen. Mike Lee notes, the House Intelligence bill is “window dressing” to “expand government surveillance.” Under the House Intelligence Committee’s bill, the FBI might continue practices that led to batch queries of current and former federal government officials, journalists, political commentators, and 19,000 donors to a congressional campaign. Another expansion in the bill is its restoration of “Lone Wolf Surveillance” authority, the suspicionless monitoring of online searches, social media usage, and increasingly unique biological traits such as facial recognition, DNA, and even analysis of body language to catch the solitary terrorist. ACLU’s Matthew Harwood wrote in 2015 that this approach “would represent a fundamental assault on a free society. Such ‘countermeasures’ should send a shiver down your spine … The dangers to Americans in allowing government agencies to collect such intimate information in order to discover whether any of them are possible lone wolves should be obvious in terms of the destruction of privacy, among other things. The result would be both an Orwellian world and a hopeless one in safety terms.” Drawing on data from multiple studies, Harwood wrote: “It’s already clear that none of these expensive and advanced technological ‘solutions’ will work. Totally innocent conduct (‘false positives’) will overwhelm the truly menacing.” Expect champions of the intelligence community to continue to pull out all the stops, from backroom legislative maneuvers to more non-reform “reform” proposals. They will continue until more Americans contact their House and Senate Members and demand passage of a real reform measure, such as the Government Surveillance Reform Act – which upholds the Constitution’s requirement for a probable cause warrant for Americans’ communications, location and vehicle data, web browsing, and search records, while allowing reasonable exceptions for cybersecurity and emergency situations. Soon, the House Judiciary Committee will also be releasing a true reform bill, as well. Let Congress know where you stand. Politico reports that the House Permanent Select Committee on Intelligence has released detailed talking points outlining that panel’s draft of its bill for Section 702 reauthorization, a Foreign Intelligence Surveillance Act authority that expires at the end of this year.
“The bill described by the House Intelligence Committee, while offering a few useful reforms, is a pallid imitation of the kind of comprehensive reform that is needed,” said Gene Schaerr, PPSA general counsel. Sen. Mike Lee put it even more bluntly, noting that “these supposed ‘reforms’ are mere window dressing and would even expand government surveillance programs.” “The House Intelligence bill only pays lip service to a warrant requirement,” Schaerr said, “applying it to the limited set of ‘evidence of a crime’ surveillance queries, while allowing the administration to continue large-scale surveillance of Americans under its utterly elastic standard of ‘foreign intelligence purposes.' Furthermore, the proposal does nothing to restrict the government’s purchasing of Americans’ most sensitive and personal data or to rein in the administration’s surveillance under executive orders.’” Schaerr said the House Intelligence bill is a political marker from a committee known for its closeness to the intelligence community. It is not widely expected to become the tentpole for Section 702 reauthorization. “Congress should look instead to a bill now being drafted by the House Judiciary Committee,” Schaerr said. “Chairman Jim Jordan and his colleagues are hard at work at crafting legislation that will offer deeper and more substantive reforms, while respecting the needs of national security.” Rep. Andy Biggs (R-AZ), who has been participating in discussions between the two committees, told Politico, “The one thing that everybody agrees on is not only do you have to take care of 702, you have to take care of the broader stuff.” “We look forward to a bill from the Judiciary Committee that does, indeed, take care of the broader stuff – including a stronger warrant requirement, closing the data broker loophole, and the Executive Order loophole,” Schaerr said. Schaerr also pointed to the recently introduced Government Surveillance Reform Act (GSRA) as an example of what comprehensive reform of Section 702 could look like. Under the GSRA, warrants would be required to glean communications, geolocation histories, and browsing and search data – whether from Section 702 or from data purchased by federal agencies from data brokers. The GSRA effectively ends the FBI’s practice of using the “backdoor search loophole” that enables warrantless searches for specific American communications within the massive Section 702 database. And it places legal guardrails on the Administration’s use of Executive Order 12333 to surveil Americans. “Unlike the House Judiciary Committee and the GSRA reform efforts, the House Intelligence Committee’s proposal is deeply inadequate and will surely not satisfy the vast majority of Members in the House and Senate who want comprehensive, substantive reforms to the entire surveillance state, not just to FISA and Section 702,” Schaerr said. Every now and then, even with an outlook jaded by knowledge of the many ways we can be surveilled, we come across some new outrage and find ourselves shouting – “no, wait, they’re doing what?”
The final dismissal of a class-action lawsuit law by a federal judge in Seattle on Tuesday reveals a precise and disturbing way in which our cars are spying on us. Cars hold the contents of our texts messages and phone call records in a way that can be retrieved by the government but not by us. The judge in this case ruled that Honda, Toyota, Volkswagen, and General Motors did not meet the necessary threshold to be held in violation of a Washington State privacy law. The claim was that the onboard entertainment system in these vehicles record and intercept customers’ private text messages and mobile phone call logs. The class-action failed because the Washington Privacy Act’s standard requires a plaintiff to approve that “his or her business, his or her person, or his or her reputation” has been threatened. What emerged from this loss in court is still alarming. Software in cars made by Maryland-based Berla Corp. (slogan: “Staggering Amounts of Data. Endless Possibilities”) allows messages to be downloaded but makes it impossible for vehicle owners to access their communications and call logs. Law enforcement, however, can gain ready access to our data, while car manufacturers make extra money selling our data to advertisers. This brings to mind legislation proposed in 2021 by Sens. Ron Wyden (D-OR) and Cynthia Lummis (R-WY) along with Reps. Peter Meijer (R-MI) and Ro Khanna (D-CA). Under their proposal, law enforcement would have to obtain a warrant based on probable cause before searching data from any vehicle that does not require a commercial driver’s license. Under the “Closing the Warrantless Digital Car Search Loophole Act,” any vehicle data obtained in violation of this law would be inadmissible in court. Sen. Wyden in a statement at the time said: “Americans’ Fourth Amendment rights shouldn’t disappear just because they’ve stepped into a car.” They shouldn’t. But as this federal judge made clear, they do. Late last week, word began to circulate that the Senate majority is considering including Section 702 of the Foreign Intelligence Surveillance Act in a Continuing Resolution (CR). On Monday morning, a broad coalition of civil liberties groups – left, right and center – sent a letter to Majority Leader Chuck Schumer urging him and the Senate not to include Section 702 in the CR or any must-pass legislation.
Bob Goodlatte, PPSA Senior Policy Advisor and former Chairman of the House Judiciary Committee, explained why PPSA joined in this effort in a media statement. Goodlatte said: “We’ve seen how short-term extensions have a habit of becoming long-term. Extending Section 702 in the CR risks a clean reauthorization of Section 702 with no reforms. “If that happens, expect the FBI to get back to business as usual. Expect warrantless FBI surveillance of Members of Congress and Americans exercising their First Amendment rights to continue. Including Section 702 in the CR would also cut reform off at the knees. It would short-circuit bipartisan reformers in the House and Senate, including critical legislative efforts by the House Judiciary Committee and by dozens of Senators and House Members who’ve worked in good faith to balance national security with our constitutional rights. “Upending these reform efforts would not only lead to a new wave of abuses under Section 702 or other parts of FISA – it would also enable federal agencies to increasingly surveil Americans by accessing our most sensitive personal data, scraped from apps, and sold to the government by shadowy data brokers. “For all these reasons, it would be a terrible mistake to include Section 702 in a CR or any other must-pass legislation.” Four experts on civil liberties, including PPSA’s general counsel Gene Schaerr, explored the tension between liberty and safety at a Federalist Society discussion on Section 702 of the Foreign Intelligence Surveillance Act on Friday. A newsworthy declaration was made by Beth Williams, board member of the government watchdog, the Privacy and Civil Liberties Oversight Board (PCLOB) about balancing Section 702 reform with national security. Williams called Section 702 a “highly valuable” program that “provides irreplaceable intelligence” that generates two-thirds of the president’s daily intelligence briefing. Williams added that all five PCLOB members, while disagreeing on many points, agreed that: “While Section 702 is not a bulk collections program, we agreed that reforms to the program are in order to fix some problems with its operation, particularly by the FBI and to prevent its possible misuse for political and other improper purposes. This can be done without degrading the value of the program.” This was a notable declaration given that Williams and board member Richard DiZinno had dissented from PCLOB Chair Sharon Bradford Franklin and the board’s majority on the need for warrant requirements and other reforms. Williams’ remarks validated a statement by Chair Franklin that no PCLOB member “has called for the program to lapse and also no board member has called for clean reauthorization of the program." A sharp divergence in world views emerged between the constitutional vision of Gene Schaerr and a dark, dystopian future suggested by former NSA lawyer Stewart Baker. Schaerr kicked off this part of the discussion by asking the Federalist Society audience to conduct a thought experiment by imagining what James Madison would say if we could bring him up back to life and up to speed about the many ways the FBI has to surveil Americans. “He would be horrified,” Schaerr said by the denigration of the Fourth Amendment and the breakdown between congressional and executive powers. Schaerr imagined Madison reminding us that the founders “decided that way we set up this government would be to accept some inefficiencies as the price of freedom.” Baker posited a world in which artificial intelligence enables anyone who wants to develop more lethal toxins and infectious diseases to do so, a world of weapons of mass destruction in the hands of “disgruntled teenagers.” Baker’s reply to Schaerr’s thought experiment: “I don’t think James Madison would come back and say, ‘well, you’re just going to have to live in my world and suffer 21st century consequences.’” Gene Schaerr listed the “multipronged” ways the FBI can surveil Americans – from Section 702 information, to personal, sensitive data scraped by apps and purchased by the FBI and other government agencies from data brokers, to executive orders that allow the government to extract Americans’ texts, emails, and browsing histories from the cloud. Given the pervasive reach of such government surveillance, are the alarming fears of technology and hostile actors reason to give up on the Constitution and live in a surveillance state? This discussion leaves us to decide: Do you agree with Stewart Baker, that we must embrace pervasive surveillance to survive? Or do you agree with Gene Schaerr, who concluded: “We can realign federal government surveillance powers with the founders’ vision of what our government can be.” Watch: Well, that didn’t take long.
Before a bipartisan, bicameral team of senators and representatives could finish a press conference on Capitol Hill to introduce the Government Surveillance Reform Act (GSRA), the White House held a press call to declare President Biden’s intention to veto the bill. The White House press call – a “pre-butt” (as in pre-rebuttal) – told reporters that the warrant requirement for querying U.S. persons was a “red line” that would result in a presidential veto. The White House said that it was taking this stand to make it clear that the bill would undermine U.S. security in unprecedented ways. Yet John Sakellariadis of Politico reported that the unnamed White House official also conceded on the call he and his White House colleagues “hadn’t even read the bill yet.” Sakellariadis seemed surprised by the Biden Administration’s brushoff of a very detailed and thoughtful bill. He had reported that the GSRA “actually includes carve-outs for emergencies, ‘defensive’ cybersecurity queries, emergencies, and consent.” There didn’t seem to be any recognition by the White House that Sens. Ron Wyden and Mike Lee, and Reps. Warren Davidson and Zoe Lofgren, had worked hard to try to address the administration’s legitimate national security concerns. “Joe Biden wants to veto our bipartisan government surveillance reform bill, because apparently illegal spying on American citizens is very important to his administration,” Sen. Lee shot back. “And he hasn’t even read the bill yet!” The White House, acting on bad advice from the intelligence community, has consistently taken a ham-handed approach, brushed aside any talk of compromise, and insisted on a clean reauthorization of Section 702 of the Foreign Intelligence Surveillance Act. That authority, enacted by Congress for foreign surveillance but often used by federal agencies to surveil Americans, expires at the end of this year. That dynamic alone gives reformers the strategic upper hand to demand changes. Worse for the Administration, Members of Congress from both sides of the aisle say they are hearing a lot from constituents who are hopping mad about warrantless surveillance, as well as having their sensitive, personal data purchased by the government from shady commercial data brokers. It should occur to the Biden Administration that against this backdrop of discontent – and with the pending expiration of Section 702 – that the White House is doubling down on a weak hand. This seems like bad politics. It is certainly bad policy. The Ninth Circuit Court of Appeals in March issued a controversial opinion in Twitter v. Garland that the Electronic Frontier Foundation calls “a new low in judicial deference to classification and national security, even against the nearly inviolable First Amendment right to be free of prior restraints against speech.”
X (née Twitter) is appealing this opinion before the U.S. Supreme Court. Whatever you think of X or Elon Musk, this case is an important inflection point for free speech and government surveillance accountability. Among many under-acknowledged aspects of our national security apparatus is the regularity with which the government – through FBI national security letters and secretive FISA orders – demands customer information from online platforms like Facebook and X. In 2014, Twitter sought to publish a report documenting the number of surveillance requests it received from the government the prior year. It was a commendable effort from a private actor to provide a limited measure of transparency in government monitoring of its customers, offering some much-needed public oversight in the process. The FBI and DOJ, of course, denied Twitter’s efforts, and over the past ten years the company has kept up the fight, continuing under its new ownership. At issue is X’s desire to publish the total number of surveillance requests it receives, omitting any identifying details about the targets of those requests. This purpose is noble. It would provide users an important metric in surveillance trends not found in the annual Statistical Transparency Report of the Office of the Director of National Intelligence. Nevertheless, in April 2020, a federal district court ruled against the company’s efforts at transparency. In March 2023, the Ninth Circuit upheld the lower court’s ruling, sweeping away a substantial body of prior restraint precedent in the process. Specifically, the Ninth Circuit carved out a novel exemption to long established prior restraint limitations: “government restrictions on the disclosure of information transmitted confidentially as part of a legitimate government process.” The implications of this new category of censorable speech are incalculable. To quote the EFF amicus brief: “The consequences of the lower court’s decision are severe and far-reaching. It carves out, for the first time, a whole category of prior restraints that receive no more scrutiny than subsequent punishments for speech—expanding officials’ power to gag virtually anyone who interacts with a government agency and wishes to speak publicly about that interaction.” This is an existential speech issue, far beyond concerns of party or politics. If the ruling is allowed to stand, it sets up a convenient standard for the government to significantly expand its censorship of speech – whether of the left, right or center. Again, quoting EFF, “[i]ndividuals who had interactions with law enforcement or border officials—such as someone being interviewed as a witness to a crime or someone subjected to police misconduct—could be barred from telling their family or going to the press.” Moreover, the ruling is totally incongruous with a body of law that goes back a century. Prior restraints on speech are the most disfavored of speech restrictions because they freeze speech in its entirety (rather than subsequently punishing it). As such, prior restraint is typically subject to the most exacting level of judicial scrutiny. Yet the Ninth Circuit applied a lower level of strict scrutiny, while entirely ignoring the procedural protections typically afforded to plaintiffs in prior restraint cases. As such, the “decision enables the government to unilaterally impose prior restraints on speech about matters of public concern, while restricting recipients’ ability to meaningfully test these gag orders in court.” We stand with X and EFF in urging the Supreme Court to promptly address this alarming development. The Government Surveillance Reform Act (GSRA) Four bipartisan champions of civil liberties – Sen. Ron Wyden (D-OR), Sen. Mike Lee (R-UT), Rep. Warren Davidson (R-OH) and Rep. Zoe Lofgren (D-CA) – today introduced the Government Surveillance Reform Act (GSRA), legislation that restores force to overused Capitol Hill adjectives like “landmark,” “sweeping,” and “comprehensive.”
“The Government Surveillance Reform Act is ambitious in scope, thoughtful in its details, and wide-ranging in its application,” said Bob Goodlatte, former Chairman of the House Judiciary Committee and PPSA’s Senior Policy Advisor. “The GSRA is a once-in-a-generation opportunity for wide-ranging reform.” The GSRA curbs the warrantless surveillance of Americans by federal agencies, while restoring the principles of the Fourth Amendment and the policies that underlie it. The authors of this bill set out to achieve this goal by reforming how the government uses three mechanisms to surveil the American people.
The GSRA will rein in this ballooning surveillance system in many ways.
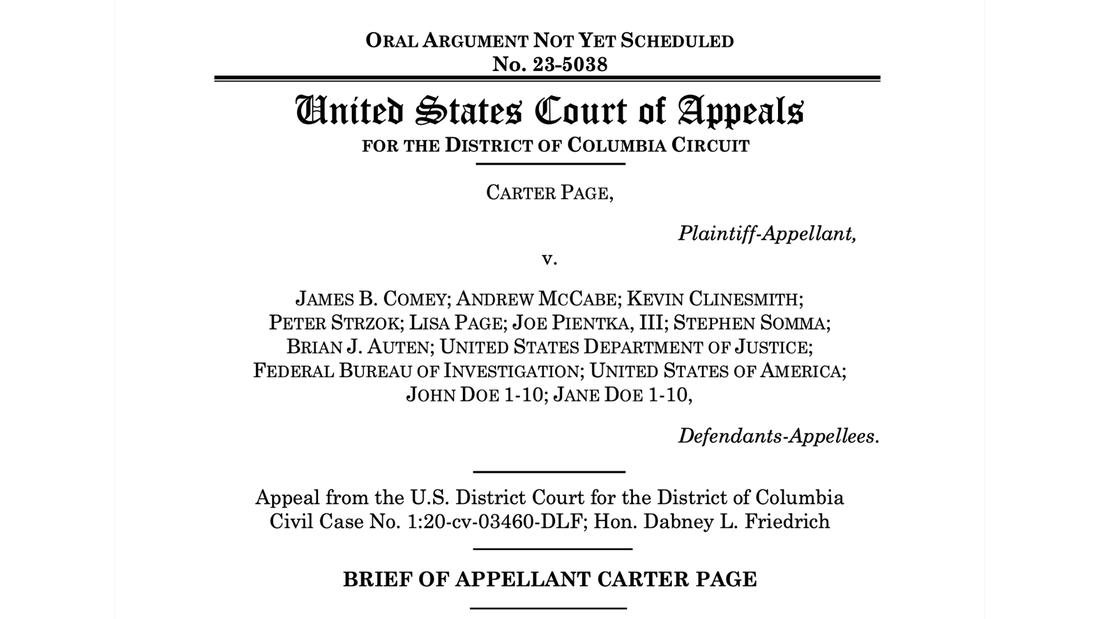
“The GSRA enjoys widespread bipartisan support because it represents the most balanced and comprehensive surveillance reform bill in 45 years,” Goodlatte said. “PPSA joins with a wide-ranging coalition of civil liberties organizations to urge Congress to make the most of this rare opportunity to put guardrails on federal surveillance of Americans. “We commend Senators Wyden and Lee, and Representatives Davidson and Lofgren, for writing such a thorough and precise bill in the protection of the constitutional rights of every American.” “Health of Democracy at Stake""The president and the general counsel of PPSA late last night asked the U.S. Court of Appeals for the District of Columbia to reverse a lower court ruling that prohibited Carter Page from suing eight federal officers who played a direct role in his illegal surveillance during the now-infamous “Crossfire Hurricane” investigation. The appeal filed by Erik Jaffe and Gene Schaerr of the Schaerr-Jaffe law firm seeks a private right of action against former FBI Director James Comey, former deputy director Andrew McCabe, and former FBI agent Peter Strzok, former FBI lawyers Lisa Page and Kevin Clinesmith, as well as three others in the FBI and Department of Justice. As described by the Justice Department’s Inspector General’s investigation into the Crossfire Hurricane case, these officials relied on the false Steele report, concocted by an opposition researcher with ties to the political party opposing Trump, in order to portray Page as a Russian agent. The defendants hid from the court the FBI’s internal misgivings about the Steele report, and CIA warnings about its reliability. These untruths were used to support four separate surveillance requests, deceiving the secret Foreign Intelligence Surveillance Act (FISA) court. Clinesmith later pled guilty to a felony false statement charge for doctoring a document from the CIA attesting that Carter Page was an operational contact and asset of the agency to state that Page was “not a source.” The appeal on behalf of Page asks the court to consider errors in the lower district court’s ruling, which dismissed Page’s claims without any discovery. The appeal notes that the plain language of FISA allows an aggrieved person to sue if that victim has suffered from the unlawful abuse of that authority. FISA makes it illegal to use or disclose information obtained by such illicit surveillance. The appeal also rests on the PATRIOT Act, which makes it unlawful for federal officers or employees to use or disclose such information except for lawful purposes. The appeal reads:
“This case is about holding government actors accountable for their plainly illegal conduct of using fraud and deceit to obtain secret search warrants against an innocent citizen. Worse still, such tactics were used against an innocent foreign policy advisor to a disliked presidential campaign in a transparently political effort to derail that campaign.” As a result of official leaks, Carter Page for months was derided in the mass media as a “traitor.” And that, according to attorney Gene Schaerr, was a grave injustice perpetrated by senior FBI officials: “You don’t have to be a fan of Donald Trump to understand that an FBI that uses concocted criminal accusations to try to skew a presidential election is a menace to democracy. Reversal of the lower court’s decision is necessary to restore accountability for the kinds of unlawful surveillance and explicit election interference engaged in by the FBI officials here. These powers should never be used against any candidate – whether establishment or populist, left or right. “Reversal of the lower court is also necessary to restore the nation’s trust in intelligence gathering. It is astounding that the same intelligence community that tells Congress to reauthorize FISA’s Section 702 without reforms also waves away the Carter Page scandal, telling us, ‘nothing to see here, folks.’ If Congress reauthorizes Section 702, it should also reform that surveillance program as well as those that were abused to harm Dr. Page. The health of our democracy is at stake.” When FBI Director Christopher Wray came under heated questioning during his testimony Tuesday before the Senate Homeland Security and Governmental Affairs Committee, he let slip a remark likely to haunt him for the rest of the debate over proposed reforms to Section 702 of the Foreign Intelligence Surveillance Act (FISA).
Director Wray said, “With everything going on in the world, imagine if a foreign terrorist overseas directs an operative to carry out an attack here on our own backyard, but we’re not able to disrupt it because the FBI’s authorities have been so watered down.” By “watered down” Wray meant reformers’ proposal requiring the FBI to meet the Fourth Amendment’s requirement to obtain a probable cause warrant before accessing the private communications of Americans taken from Section 702. This authority was enacted by Congress to enable surveillance of foreign terrorists and spies located on foreign soil. There is no reason why Section 702 cannot be used to surveil “a foreign terrorist overseas.” The problem is that this authority has become a prime resource for the FBI and other agencies to warrantlessly review the information of Americans. Sen. Rand Paul (R-KY), Ranking Member on the committee, responded: “You would think we’d be going after foreigners, but we are using the Foreign Intelligence Surveillance Act to go after Americans.” In addition to skepticism from Sen. Paul and others on the committee, Director Wray’s assertions are contradicted by others with experience in FISA. In a recent editorial, Sharon Bradford Franklin, chair of the independent government watchdog group, the Privacy and Civil Liberties Oversight Board (PCLOB), with two other board members in a recent Washington Times editorial, supported requiring a court order or warrant before the government can review Americans’ Section 702 data. The PCLOB members noted that “the FBI has repeatedly violated querying rules to run searches on Americans. This includes impermissible searches for members of Congress, those who protested the murder of George Floyd, preachers, participants in an FBI community relations program, victims who reported crimes …The FBI has failed to get this right for more than a decade. The bureau’s persistent noncompliance over the years dramatically illustrates the need for independent, impartial, and external review. These compliance errors may also undermine the public’s trust in the FBI, raising real questions about its ability to police itself.” In his written testimony, Director Wray also informed the committee that a warrant requirement would amount to a “de facto ban” on U.S. person queries because warrants are so difficult to obtain from a court. Would a warrant requirement necessarily be a “ban” that would “water down” the FBI’s ability to protect Americans? David Aaron, who held several senior legal positions at the Department of Justice’s National Security Division, wrote in Just Security that “requiring the government to establish probable cause and obtain judicial approval before searching for U.S. person’s communications within previously collected material would bolster that confidence and is a relatively light burden on the government.” A majority in Congress clearly agree. None other than Senate Judiciary Chairman Dick Durbin (D-IL) has said he will only support Section 702 reauthorization if there are “significant reforms,” including “first and foremost, addressing the warrantless surveillance of Americans in violation of the Fourth Amendment.” Or, as Chair Franklin and her colleagues wrote: “We do not permit the police to break into a home without such court approval, and we should not permit government personnel to access our communications through U.S. person queries without court review. This is Civics 101.” Sen. Paul told Wray: ”I fear that our federal government is still undertaking many of the same tactics that the Church Committee found to be unworthy of democracy.” Perhaps it is the Fourth Amendment that has been watered down. Did IRS Inspect Personal Data of Matt Taibbi and Other Journalists?Matt Taibbi is not everyone’s cup of tea – or shot of tequila. He is a former Rolling Stones reporter, an investigative journalist with gonzo-flavored prose. Taibbi was most recently in the headlines for reporting on government interference, including FBI agents, in secretly advising social media content curation. This was just one of the revelations of the Twitter Files.
That data dump, released by X CEO Elon Musk, show considerable interaction between the federal government and social media companies’ curation of ideological content. Whether this was “jawboning” or “coercion” on the part of the government will be at the heart of an upcoming U.S. Supreme Court case, Murthy v. Missouri. This is an intensely political case, one that pits the Biden Administration, which insists it has every right to alert social media companies about misinformation, against Republicans, who see it as secret censorship. A new report from the House Judiciary Committee raises the question why the IRS sent an agent to make an unannounced field visit to the home of journalist Matt Taibbi. That visit just happened to occur on the same day Taibbi was testifying before Congress about purported secret government abuse to dial back or exclude content from social media. The Weaponization of the Federal Government subcommittee found that the IRS had taken the unusual step of opening a case against Taibbi on Christmas Eve, a Saturday, just weeks after Matt Taibbi began reporting on the Twitter Files. In the four-and-one-half years between when the IRS alleges it last tried to contact Taibbi about his taxes and the day it conducted an unannounced field visit, neither he nor his accountant received notice from the IRS about an issue with his tax returns. As it turned out, the journalist owed no money to the IRS, but the IRS did owe him a refund. As a result of this and similar incidents, IRS chief Danny Werfel repealed the agency’s policy of allowing agents to make unannounced field visits to taxpayers’ home. In today’s social media-saturated world, the appearance of an IRS agent acting as a government “heavy” to pressure a journalist – if that is what indeed happened – is a tactic guaranteed to backfire. The greater danger is how the IRS could misuse its immense surveillance power for its own ends or those of one political master or another. The IRS, like many other federal agencies, purchases Americans’ personal data scraped from our apps and sold to it by third-party data brokers – a major focus in reforms that civil libertarians want to add to FISA’s Section 702. The IRS could have easily accessed Taibbi’s personal location history, as well as his communications from emails to texts, all without a warrant. A good follow up question for Congress might be to ask the IRS if it used purchased data to snoop on Taibbi or other journalists. The IRS does not need probable cause to investigate us. It doesn’t need a warrant to send someone to our home, to order us to conduct an expensive and time-consuming audit, or to look into our most personal and sensitive information taken right out of our smartphones. Congress should demand to know if the IRS or any other government agency has been accessing the personal data of journalists investigating the administration. Is the Executive Branch Targeting Oversight Committees? PPSA continues to press a Freedom of Information Act (FOIA) request seeking documents that would shed light on the extent to which the executive branch is spying on Members of Congress. We are asking the government for production of documents on “unmasking” and other forms of government surveillance of 48 current and former House and Senate Members on committees that oversee the intelligence community.
Now the court and Congress have fresh reason to give the issue of executive branch spying on Congress and its oversight committees renewed attention. Jason Foster, the former chief investigative counsel for Sen. Chuck Grassley – the Ranking Member of the Senate Judiciary Committee – recently learned that he is among numerous staffers, Democrats as well as Republicans, who had their personal phone and email records searched by the Department of Justice in 2017. A FOIA request filed by the nonprofit Empower Oversight, founded by Foster, seeks documents concerning the government’s reasons for compelling Google to reveal the names, addresses, local and long-distance telephone records, text message logs and other information about the accounts of congressional attorneys who worked for committees that oversee DOJ. The government’s subpoena also compelled the release of records indicating with whom each user was communicating. The Empower Oversight FOIA notes: “This raises serious public interest questions about the basis of such intrusion into the personal communications of attorneys advising congressional committees conducting oversight of the Department. Constitutional separation of powers and privilege issues raised by the Speech or Debate Clause of (U.S. Const. art I. § 6) and attorney-client communications of those targeted with these subpoenas should have triggered requirements for enhanced procedural protections and approvals.” As The Wall Street Journal noted in an editorial, these subpoenas coincided with leaks of classified information concerning a wiretapped phone call between incoming Trump national security adviser Michael Flynn and the Russian ambassador. This leak was investigated by the Senate Judiciary Committee. Many now wonder if DOJ’s dragnet of personal information of congressional staffers was an attempt at misdirection, perhaps a fishing expedition to find someone else to blame. Empower Oversight’s FOIA states: “If the only reason the Justice Department targeted the communications of these congressional attorneys was their access to classified information that was later published by the media, it raises the question of whether the Department also subpoenaed the personal phone and email records of every Executive Branch official who had access to the same information.” The Empower Oversight FOIA concludes about this surveillance of Congressional staff: “It begs the question whether DOJ was equally zealous in seeking the communications records of its own employees with access to any leaked document.” Sen. Grassley, who aggressively pursues government surveillance overreach, will likely want to follow up on these questions. In the meantime, PPSA petitions the D.C. Circuit Court for an en banc hearing on the possible unmasking and other surveillance of some of the elected bosses of these congressional attorneys. Case Involves “Unmasking” and “Upstreaming” of 48 Members of Congress Earlier this week, PPSA asked the D.C. Circuit court to require federal agencies to follow FOIA’s most basic requirement: conduct a search for records. Although that should be simple enough, agencies have been excusing themselves of that obligation at an alarming rate, and PPSA has asked the court to rein in this practice.
PPSA’s request this week for an en banc hearing follows up on a FOIA request PPSA submitted in 2020 to six agencies – the Department of Justice and the FBI, the Office of the Director of National Intelligence, the National Security Agency, the Central Intelligence Agency, and the Department of State. PPSA sought records from these agencies about the possible surveillance of 48 Members of Congress who serve or served on intelligence oversight committees. The request specifically concerns two intelligence practices under the Foreign Intelligence Surveillance Act (FISA). One such practice is “unmasking,” which results in the naming of Americans caught up in foreign surveillance in U.S. intelligence summaries. The other practice is “upstreaming,” the use of a person’s name as a search term in a database. Targets include prominent current and former House and Senate Members, including Sen. Marco Rubio, Rep. Mike Turner, Rep. Adam Schiff, as well as now-Vice President Kamala Harris and former Secretary of State Mike Pompeo. “Their silence speaks volumes,” Gene Schaerr, PPSA general counsel said at the time. “They clearly do not want to answer our requests.” Last year, the district court invoked the judicially created Glomar doctrine, which allows agencies to neither confirm nor deny the existence of records relating to matters critical to national security. In doing so, the district court relied on the D.C. Circuit’s expansion of the Glomar doctrine in Wolf v. CIA (2007) and Electronic Privacy Information Center (EPIC) v. NSA (2012), which allows agencies to refuse to confirm or deny the existence of records without even searching first to determine if any records might exist. In both instances, the federal court allowed the government to skip the search requirement in the text of the Freedom of Information Act. PPSA is now petitioning the court to reconsider this ruling with an en banc hearing with the court. “FOIA’s plain text requires federal agencies to search for responsive records before determining what information they may properly withhold, even in the Glomar context,” PPSA declares. “Wolf and EPIC are untenable in the face of intervening Supreme Court precedent, and they clash with at least three other circuits that, even in Glomar cases, reject deviating from the demands of FOIA’s plain text.” In short, PPSA is alerting this federal court how far it has strayed from precedent and the law. Glomar began as a judicial solution to protect the most sensitive secrets of the nation. In the original case, Glomar protected secrets involving the CIA’s raising of a sunken Soviet nuclear submarine. It has since been expanded to prevent the searching of records; an inherently absurd proposition given that agencies cannot even make a Glomar determination without looking. And Glomar is now reflexively used to plainly defy FOIA, a law that mandates searches. PPSA will report on the court’s response. Long Lake Township v. Maxon In a brief before the Michigan Supreme Court, PPSA alerted the court to the danger of intimate searches of home and residents by relatively inexpensive drones now on the market.
Commercially available drones have thermal cameras that can penetrate beyond what is visible to the naked eye. They can be equipped with animal herd tracking algorithms that can enhance the surveillance of people. Drones can swarm and loiter, providing round-the-clock surveillance. They can carry lightweight, cell-site simulators that prompt the mobile phones of people inside the targeted home to give up data that reveals deeply personal information. Furthermore, PPSA’s brief states that drones “can see around walls, see in the dark, track people by heat signatures, and recognize and track specific people by their face.” These are some of the ramifications of a case now before the Michigan Supreme Court. This case began when Long Lake Township in Michigan, suspecting that Todd and Heather Maxon had violated an agreement not to add to a scrap pile of old cars on their five-acre estate, hired a private drone photography business to investigate. No warrant was issued for this surveillance. Michigan’s top court is now reviewing the ruling by a lower court that found that while warrantless drone surveillance of a residence violated the Fourth Amendment, the evidence should not be excluded from this civil case. PPSA argues that this lack of exclusion of tainted evidence threatens to open a Pandora’s box of pervasive surveillance that could pierce the privacy of virtually anyone inside any structure. PPSA cites ample precedent for the exclusion of the Maxon evidence. In Carpenter v. United States (2018), the U.S. Supreme Court made it clear that the Fourth Amendment applies to digital technologies. In that case, the Court excluded location information derived without a warrant from mobile phones. In Kyllo v. United States (2001), the Court found that the use of thermal images – which reveals the heat signature emanating from inside a home – requires a warrant. Compare Kyllo’s comparatively mild surveillance to the “stereo-camera” configuration of many commercially available drones that enable reconstruction of 3D images from 2D cameras. Such surveillance goes well beyond Kyllo, in which police simply used heat radiating from the external surface of the house to detect marijuana cultivation. “Ready-made drone packages, specifically designed for thermal surveillance flights, with the ability to create 3-dimensional maps from their footage, can be had for around $6,000,” PPSA informed the court. “For less than $10,000, police can obtain a specialized drone with superhuman sensory abilities and better maneuverability than a multi-million-dollar helicopter or plane,” PPSA told the court. Drone’s warrantless extraction of personal information far exceeds the Carpenter warrant requirement. PPSA’s filing addresses an error by the lower court. The Michigan Court of Appeals recognized that the Township had violated the Fourth Amendment in its use of drones. That court nonetheless found that the exclusionary rule did not apply in Maxon. PPSA declared: “The Exclusionary Rule is a judicially crafted remedy that gives teeth to the Fourth Amendment by excluding illegally obtained evidence when the privacy value of enforcing Constitutional rights outweighs social harm from excluding evidence.” PPSA concluded: “If the Fourth Amendment is to have any real meaning in this context, evidence obtained by illegal drone surveillance must be subject to exclusion.” The Michigan Supreme Court is hearing oral argument on this case this week. PPSA will follow the outcome of this important, precedent-setting case. The Colorado Supreme Court issued a 5-2 ruling that leaves an urgent privacy question wreathed in a cloud of ambiguity. As a result, Americans must worry that merely being in the same location as someone who might have done an internet search for suspicious material could end up with their own search data being examined by the police.
So-called “reverse warrants” are a powerful new type of search warrant enabled by the collection of Americans’ private data. Reverse warrants allow the police to sift through the search histories of thousands of people. They come in two types: geofence warrants, which allow police to identify people whose devices were in a certain area at a certain time, and reverse keyword warrants, which allow police to identify who searched certain keywords, phrases, or addresses online. These warrants and their underlying technologies allow police to track any person and search through their data. Instead of developing suspicions about a person based on factual evidence and then applying for a warrant to search that specific person – as required by the Fourth Amendment – reverse warrants involve looking through the search history or location history of many innocent people in the hopes of finding a suspect. Reverse warrants exist in legal limbo. There is little precedent or written law that govern this new form of data analysis. Accordingly, some courts have treated reverse warrants as they would any standard warrant. Seymour v. Colorado is the first case to address the constitutionality of reverse warrants. This case springs from a particularly heinous crime – an arson that killed a family of five. Two months later, the Denver Police Department obtained a reverse keyword warrant. As a result of the warrant, Google was forced to hand over the data of eight people, five of whom had Colorado-based IP addresses that had searched for the location of the arson in a two-week period before the crime. Three suspects were eventually charged. One of them, Gavin Seymour, sued to suppress evidence obtained by the warrant on constitutional grounds. The court held that “Seymour has a constitutionally protected privacy interest in his Google search history,” and that “Seymour’s Google search history implicates his right to freedom of expression.” The court also found that law enforcement obtained and executed the warrant in good faith, so the evidence shouldn’t be suppressed under the exclusionary rule. Thus the court acknowledged the serious constitutional issues at play and still treated the reverse warrant as if it was just an ordinary search. The court stated that “the warrant required individualized probable cause and that its absence here rendered the warrant constitutionally defective.” Yet, somehow, it was still admissible evidence. Five innocent people had their data searched. Another five innocent people were murdered in a fire. There is a lot at stake in this case, and a lot to unpack. Does a search of Google search histories by a given address satisfy the Constitution’s requirement for a particularized search? Can probable cause be asserted when the identity of the suspect is unknown? Could digital bystanders have evidence used against them from a search result unrelated to this particular crime? Perhaps this case will advance to the U.S. Supreme Court, which could take this opportunity to articulate boundaries and rules for future searches. We’ve seen, however, a time lag in the Court’s addressing of new technologies. Congress should consider taking measures to protect privacy in reverse warrants before the Supreme Court is forced to weigh in. Shameless Opportunism...The intelligence community is now spinning the media that the barbarous invasion of Israel and mass murder of its citizens by Hamas should prompt Congress to reauthorize Section 702 of the Foreign Intelligence Surveillance Act without any meaningful changes or reforms.
Before listening to the intelligence community’s spin, Congress should first ask why given this powerful Section 702 authority and all the technology in the hands of the NSA, did U.S. intelligence miss the scale and scope of Hamas’ intentions? While U.S. intelligence detected rising activity in Gaza, it did not detect the threat that resulted in the killing of more than 1,400 Israelis and at least 30 Americans. Instead of explaining this abject intelligence shortfall, some in the intelligence community are defaming champions of Section 702 reform on Capitol Hill as opposing surveillance of Hamas. This weak attempt to deflect from an abject failure makes no sense. It is, at best, an especially callous perversion of Rahm Emanuel’s aphorism that one should “never let a good crisis go to waste.” Carrie Cordero, a CNN legal and national security analyst, and former counsel at the Office of the Director of National Intelligence, writes: “Hamas, Hezbollah and their state-sponsor, Iran, are wholly appropriate intelligence targets, and Section 702 authority should not be degraded while threats from these actors have escalated to the degree of starting a new war in the Middle East.” In just a few words, Cordero portrays the many House and Senate Members in both parties who are pushing to add warrants for Americans to the reauthorization of Section 702 as being willing to “degrade” an authority that counters some of the worst regimes in the world. This broadside obfuscates the purpose of Section 702 and how it is being misused by our government to spy on the American people. Congress designed Section 702 to create a legal authority for U.S. intelligence agencies to spy on foreigners located abroad for national security purposes. It is, as Cordero notes, a tool especially designed for counterterrorism. No reform on the table would restrict U.S. intelligence from using Section 702 to surveil Hamas, Hezbollah, Iran, Russia, China, North Korea, or the devil himself. So how, then, could reforms to Section 702 “degrade” this important and useful authority? There can be only one meaning to this phrase. Somehow, protecting the rights of American citizens against intrusive and unconstitutional spying would “degrade” Section 702. Civil liberties groups and their champions on the Hill are concerned that this authority, meant to surveil foreign threats on foreign soil for national security, has been used by the FBI to spy on a Member of the U.S. House, a Member of the U.S. Senate, 19,000 donors to a congressional campaign, community leaders, and protest groups both left and right. The FBI also uses Section 702 to warrantlessly access the communications of Americans to obtain a backdoor route to prosecuting them for ordinary crimes, such as bribery and healthcare fraud – far beyond the intention of Congress in passing Section 702. In the hands of the FBI, Section 702 has turned the Fourth Amendment requirement for a probable cause warrant for American citizens into vaporware. Fixing this would do nothing to degrade the ability of the CIA to follow Hamas and Hezbollah, or to restrain the FBI from obtaining a warrant to surveil an American who is in communication with dangerous actors. That they now want to use their failure as an excuse to violate the civil liberties of law-abiding U.S. citizens – by the hundreds of thousands each year – speaks to shameless opportunism, masking incompetence and authoritarian tendencies. Congress passed a mandate in 2021 that will require all new cars sold later in this decade to have a built-in drunk driver detection system. This law, well-intentioned as it may be, is fraught with enormous risks to the privacy of any American who drives a car.
The vague goal this mandate sets out is: If your car thinks you’re overserved, your car won’t start. Or perhaps it will pull over and call the police. It is not clear, exactly, how this technology will work. In any event, this law promises to make every car a patrol car, with you inside it. Rep. Thomas Massie (R-KY), a long-time defender of civil liberties, is not having it. He is proposing an amendment to the Transportation, Housing and Urban Development (yes, the Washington acronym here is THUD) appropriations bill to safeguard Americans’ constitutional right to privacy by forbidding federal expenditures to implement this ill-conceived mandate. PPSA is proud to support this amendment and we stand together with other supporters, including FreedomWorks and the Due Process Institute. While aggressive action to curb impaired driving is appropriate, the privacy issues raised by Rep. Massie about the mandate for this “advanced drunk driving and impaired driving prevention technology” are impossible to ignore. They are ultimately of great consequence to the future of our country. First, consider that this technology will monitor the driving performance of millions of Americans who don’t drink and drive, potentially keeping many of them from operating their vehicles. While many states allow for court-mandated ignition interlock devices for people convicted of DUIs (requiring people under such an order to clear a self-administered breathalyzer test before their cars will start), these state restrictions are far more reasonably tailored than the broader and more intrusive federal mandate. Crucially, they make the necessary distinction between the irresponsible few who are under a court order, and the responsible many who are not. Additionally, the state regulations do not passively monitor drivers’ performance. What do the responsible many have to lose under the federal mandate? The driver detection mandate could violate your privacy and constitutional rights on a massive scale. Consider: Absent a breathalyzer, this technology might well – like some commercial delivery operators already do – use a camera and AI to passively monitor your body movements for signs of impairment. Moreover, would your video data be stored? And if it is stored, would camera data follow you and any passengers in the car – perhaps with a sound recording of anything that you might say to each other? (After all, analyzing voice data could be used by AI to look for the possible slurring of your words.) And if this video and/or voice data is stored, would these videos then be part of the enormous stream of data that federal agencies – from the IRS, to the FBI, to the DHS – now routinely purchase and access without a warrant? (This brings to mind an old joke: An FBI agent walks into a bar. The bartender says, “I’ve got a joke for you.” The agent replies, “heard it!”) Video analytics technology, like facial recognition software, is hardly foolproof. Would this yet-to-be-developed device read people with disabilities as being intoxicated? Would perfectly sober people register false positives and not be able to drive? Rep. Massie’s amendment would provide a much-needed sobriety check on the government’s foolhardy leap into mandating this technology. PPSA strongly urges Congress to pass the Massie amendment and protect the privacy and constitutional rights of millions of Americans. An FBI raid on the home of a Tampa-based journalist, and the seizure of his computer, hard drives, cellphone and all they contain, is raising questions about the fidelity of the Department of Justice to a year-old revision to its News Media Policy announced by Attorney General Merrick Garland. Under that policy, the Department is forbidden from using compulsory legal processes to obtain the newsgathering records of journalists, except in extreme circumstances.
Now a wide spectrum of press freedom and civil liberties organizations, including PPSA, are asking the Department of Justice to provide transparency about this FBI raid in May. The FBI executed its search warrant at the home of journalist Tim Burke, which he shares with his wife, Tampa city councilwoman Lynn Hurtak. The credibility of this extreme action is highly questionable, leaving the Department to explain how this ransacking of a journalist’s home and seizure of his devices differs from the now-widely ridiculed police raid on a newspaper in rural Kansas. NYPD’s Angwang Case This week, Baimadajie Angwang, an officer of the New York Police Department, appears before an administrative judge to make a bid to remain on the force. The long journey of Angwang – from Tibetan refugee to U.S. Marine in Afghanistan, to police officer, to accused spy – shows how an American can have his reputation destroyed and his freedom threatened by secret charges.
As a teenager, Angwang visited the United States on a cultural exchange program only to be beaten by Chinese police on his return to his homeland. He fled the country and successfully sought asylum and citizenship in the United States, serving as a Marine. Angwang joined the NYPD in 2016, married, and became a father. On the morning of Sept. 21, 2020, Officer Angwang was confronted in front of his home by four souped-up pickup trucks squealing to a halt, half-a-dozen officers in tactical gear piling out, and rifles pointed inches from his face. Angwang was charged with spying for China on his fellow Tibetans in New York and lying on a security form. Angwang was held in the Metropolitan Detention Center in Brooklyn for five months. The conditions in that jail are wretched, far worse than those of most prisons. Angwang had to borrow underwear from another prisoner. The facility lost power, leaving desperate prisoners to suffer in the cold through a bitter January. When Angwang fell ill, guards ignored his pleas for help. What was Angwang’s alleged crime? It grew out of his quest to secure a long-term visa from the Chinese consulate to visit his elderly parents in Tibet and allow them to meet their granddaughter. In extensive conversations with a consular official, Angwang had tried to get this visa by demonstrating that he was friendly and apolitical. Angwang’s lawyer, John F. Carman, wrote to a federal judge that his client tried to strike a “solicitous tone and accommodating posture.” Prosecutors said that Angwang invited Chinese consular officials to NYPD events and reported on the activities of other Tibetans in New York. The prosecution’s case was based on calls and likely texts between Angwang and the consulate, all secretly recorded. To be fair, the government arguably has good reason to watch how Chinese diplomats try to convert American citizens into spies. Furthermore, the government did obtain a warrant to surveil Angwang. Carman said that evidence from these communications, however, was misinterpreted and taken out of context by prosecutors. In court, Angwang faced a dilemma shared with many charged with evidence they are not allowed to see. In such cases, when classified evidence is introduced in a trial, the judge and prosecutors secretly determine in a sealed court what evidence can be seen by the defense attorney and what can be presented in court. In August 2022, Carman read a single-page summary of these charges in the prosecutor’s office. “What I saw was so powerful, it caused me to write the judge and ask if that’s what they have, why hasn’t there been a motion to dismiss?” Carman told The New York Times. In January, prosecutors dropped the case, citing a “holistic” assessment of the evidence and “additional information bearing on the charges.” Now Angwang is asking an administrative court to let him keep his job as a New York City police officer. If he loses his job, Angwang will have to seek another job with a resume and a reputation forever under the shadow of secret evidence. “It creates a cloud of mystery,” Carman said. “You only have to assume that this guy did stuff that was bad for the country. Which is an inference that’s easily drawn, but in this case should not have been drawn.” And should a defendant like Angwang, who escapes the crosshairs of secret evidence, sue the government for compensation, the state secrets privilege will ensure that he cannot win. The evidence against the government, you see, must remain secret. The defamatory effect, however, lives on. Is there really a good justification – the protection of sources and methods – for withholding so much of a secret case? Can the government at least issue a note of exoneration for Angwang and others when secret charges are dropped? Intelligence Community Myth: “The government is neither intentionally nor inadvertently targeting Americans for surveillance through Section 702.”
Fact: This assertion is in a Wall Street Journal op-ed on Thursday by Richard E. DiZinno and Beth A. Williams – the two dissenters from the recent critical report on Section 702 from the Privacy and Civil Liberties Oversight Board (PCLOB). This statement by DiZinno and Williams is flatly contradicted by the PCLOB report. In that report, the government owns up to intentional violations. The report states: “According to the government, there have been several examples where oversight mechanisms have identified incidents involving improper intent in seeking to circumvent or violate the procedures, related rules, or statutory requirements.”
Two of these violations are from 2022. This is important because the FBI, in announcing its new “accountability” procedures, claimed that there had been no identified instances of intentional non-compliance since 2018. We know about these four searches because they are egregious, personal misuses of Section 702 data that cannot possibly be explained away. Imagine what can happen when agents can spin serious-sounding but imagined national security justifications to look at Americans’ private data and communications. PCLOB Chair Ups Ante by Calling for Probable Cause Warrant for U.S. Person Queries What are the topline takeaways from the report from the Privacy and Civil Liberties Oversight Board (PCLOB) on Section 702 of the Foreign Intelligence Surveillance Act (FISA)?
A majority of board members of this government watchdog panel directly counter the claims of the Biden Administration and the intelligence community that a requirement for the government to seek judicial review of the private communications of Americans would be “operationally unworkable” and lead to extreme danger to national security. The report punctures the FBI’s frequent claims that having the ability to rifle through Americans’ communications without a warrant is essential to national security and protecting the United States from harm. The PCLOB majority endorses “individualized and particularized judicial review” by the FISA Court before the government can review data of U.S. citizens and legal residents. PCLOB is coming down firmly on the side of civil liberties organizations that have long argued against intelligence and law enforcement agencies being allowed to have ready access to Americans’ private data and communications, with little judicial oversight. Internal FBI Procedures Insufficient The PCLOB majority finds the internal changes by the FBI in its Section 702 procedures to be far less than what is needed to protect Americans from backdoor searches, the practice of using secretly derived information to develop a case. Moreover, these searches are generally useless, as are the FBI’s internal procedures. The report also rejects that broad categories of searches, such as so-called “defensive” searches for potential victims’ information, should be exempted from judicial review. Amici, Abouts and Unmasking The report endorses the proposal to require amici – or qualified civil liberties experts to advise the FISA Court whenever proposed investigations touch sensitive cases that implicate basic constitutional rights. The board would narrow the standards by which the government selects targets. And the board would formally restrict “abouts” collection – information in which a target is merely mentioned. Even the two board members who voted against the report found that “The U.S. Intelligence Community should adopt new rules to protect against the unmasking of U.S. Persons for political purposes.” The Chair’s Call for a Warrant Requirement Chair Sharon Bradford Franklin (see p. 226) writes that a “search through Section 702 communications data seeking information about a particular American constitutes a search under the Fourth Amendment, and current query standards are insufficient to meet constitutional requirements.” Chair Franklin notes that the FBI routinely runs searches of U.S. persons at a preliminary stages of an inquiry. The FBI “asserted that it could not meet a probable cause standard for such queries conducted at these early stages.” Nor could the FBI identify, outside the categories of “victim” or “defensive” queries, “a single criminal prosecution that relied on evidence identified through a U.S. person query.” Chair Franklin raises the ante on PCLOB’s recommendation that a FISA Court provide judicial review for U.S. person queries. “But I believe that Congress should also require a probable cause standard for FBI’s U.S. person queries conducted at least in part to seek evidence of a crime in order to fully protect Americans’ privacy and civil liberties.” Franklin writes that this is the only way to ensure such queries fully comply with the Fourth Amendment, while being consistent with criminal law in other contexts. She would explicitly adopt the standards of Carpenter v. United States (2018), in which the U.S. Supreme Court held that the police don’t need a warrant to seize a cellphone but do need a warrant to search the contents of that cellphone, which contain “the privacies of life.” She analogizes this case to the “seizure” of the incidental collection of Americans’ information under Section 702, and the need to have a warrant to search it. Chair Franklin’s conclusions, and the PCLOB’s full list of 19 recommendations, are included in the executive summary of its report. |
Categories
All
|



















 RSS Feed
RSS Feed