House Judiciary Committee Passes Protect Reporters from Exploitative State Spying (PRESS) Act7/19/2023
PPSA is pleased that the House Judiciary Committee reported H.R. 4250, the Protect Reporters from Exploitative State Spying (PRESS) Act, to the full House by a unanimous 23-0 vote.
Many reporters have had their records seized by federal prosecutors, sometimes by secret orders to cloud computing companies. This bill, long supported by PPSA and civil liberties sister organizations, would protect journalists and their sources by granting a privilege to shield confidential news sources in federal legal proceedings. It contains reasonable exceptions in cases where application of the privilege could result in serious harm. Former Rep. Bob Goodlatte, who served as Chairman of the House Judiciary Committee and now as PPSA Senior Policy Advisor, said: “Journalism and the right to report on government actions must be better protected. We’ve all seen law enforcement officials under multiple recent administrations issue secret orders to surveil the private communications of journalists. Their freedom to report on government misdeeds is critical to maintaining a free society, and I encourage the broader House of Representatives to swiftly approve this legislation, as they have in the past.” PPSA would like to extend its gratitude to Reps. Kiley and Raskin for their leadership in introducing the bill, as well as to Chairman Jordan and Ranking Member Nadler for their support in moving it through committee. The PRESS Act’s passage is the result of overwhelming bipartisan support for freedom of the press guaranteed by the First Amendment of the Constitution, as well as support for our Fourth Amendment right to privacy. We hope the full House will take up and pass this important legislation soon. In 2020, the Foreign Intelligence Surveillance Court (FISC), embarrassed by the many lapses uncovered by Department of Justice Inspector General Michael Horowitz, ordered the FBI to take steps to ensure greater consistency and accuracy in its Foreign Intelligence Surveillance Act (FISA) applications. How have the Bureau’s efforts progressed? As we reported in September of that year, the FBI was developing a new system, known as “the Bridge,” that would increase collaboration within the FBI, as well as between the FBI and the DOJ Office of Intelligence, to improve compliance with the law on surveillance. The Bridge will automatically cross-reference new data with existing data in FBI’s current case-management system, Sentinel.
The Bridge was slated to be completed around the end of 2021. Two years later, the Bridge is reportedly nearing completion and will finally be ready by the end of this year. The FISA Court ordered the FBI to provide quarterly updates about the status of the Bridge’s development. Now, PPSA has learned from documents supplied in response to Freedom of Information Act requests that the FBI has decided that it no longer wants to provide the court with updates on the development of its technology. The FBI recently delivered a motion for relief to the court to be relieved from having to submit these two-page reports. Instead, the FBI wants to notify the court whenever “the Bridge has completed its long-term testing and has been fully implemented,” or when “there are any substantive updates to report.” This mode of reporting is not a good sign for the court’s imposition of an oversight obligation on the FBI, allowing the Bureau to decide when and how it wants to comply with the FISA Court. Thus, a quarterly two-page report constitutes an unbearable onus for the FBI. When the Bridge is already years late and the FBI has a track record of failing to hold itself accountable, can we really trust the agency to do its due diligence without renewed oversight? Last month, we wrote about a surprisingly frank report from the Office of the Director of National Intelligence admitting the government’s increasing role in utilizing Commercially Available Information about United States citizens for investigative purposes. Despite the Supreme Court’s ruling in Carpenter v. United States, which held that a warrant is required before the government can seize location history from cell-site records, the report candidly reveals that the bulk collection of Americans’ private data continues unabated. Now, the Commonwealth of Massachusetts is taking steps to ban the purchase and sale of location data altogether. It’s a blunt solution to a complex issue, and a bellwether for where this debate might be headed.
“Location data” refers to information about the geographic locations of mobile devices like smartphones or tablets. When collected, this data can be used for relatively benign purposes like marketing – but also to identify the movements of individuals and discern their identities (a 2013 study found that only four spatio-temporal data points are required to identify someone in most circumstances). A host of companies collect this information, package it, and sell it to private actors like advertisers – and, increasingly, law enforcement agencies. The government can learn a lot about you based on your movements – and they know it. For example, the FBI has its own team dedicated to analyzing cell tower data. A growing number of states are now taking action to protect the digital privacy of their residents. Laws passed in California and Virginia require the affirmative consent of consumers before geolocation data can be used for specified purposes. The European Union has gone further, prohibiting the use of sensitive data by default unless a company can demonstrate that its use falls under a specifically enumerated exemption. In the United States, Massachusetts’ Location Shield Act (H.357|S.148) is by far the most comprehensive effort yet to protect our data from unwarranted (or warrantless) snooping. The bill’s drafters couch it within a social policy framework; it’s described as “An Act protecting reproductive health access, LGBTQ lives, religious liberty, and freedom of movement by banning the sale of cell phone location information.” Such concerns are not unfounded. As the ACLU writes, “In the aftermath of the Supreme Court’s Dobbs decision…journalists found that data brokers have continued to buy, repackage and sell the location information of people visiting sensitive locations including abortion clinics. This puts people who seek or provide care in our state at risk of prosecution and harassment, creating a vulnerability in our state’s post-Roe protections.” Beyond addressing those concerns, however, the bill does a lot to broadly reinforce our Fourth Amendment rights against unreasonable searches and seizures, implementing a warrant requirement for any law enforcement access to location data. Such restrictions would clear away some of the murk surrounding this issue in the wake of the Carpenter case, which required a warrant when accessing location data from phone companies, but which holds limited relevance when such data are readily available for commercial purchase. (Obviously, the same legal reasoning should apply.) Americans are waking up to the dangers of the $16 billion data brokerage industry. In Massachusetts, 92% of survey respondents said the government should enshrine stronger protections for consumer data – all the way back in 2017. Whether this bill makes it over the finish line or not, it’s a clear sign that Americans want comprehensive data privacy reform. And Massachusetts’ solution is one we’ll readily share. PPSA previously sent an appeal to every Member of the U.S. House urging them to vote for the Davidson-Jacobs Amendment to the National Defense Authorization Act (NDAA). It would place significant restrictions on the government’s purchase of Americans’ Fourth Amendment-protected sensitive, personal information without a warrant.
We attached to our letter the endorsement of this measure from more than 40 civil liberties allies—ranging from the ACLU to FreedomWorks, from the Brennan Center and Demand Progress to Americans for Prosperity and the Due Process Institute. The strong bipartisan support in the House led to the passage of this important measure by voice vote. “This vote is vital because our digital histories reveal our personal lives—where we’ve been, who we’ve met or communicated with, what we’ve searched for online, even our medical issues,” we wrote. “A digital portrait can be more personal and intimate than a diary. “Yet, under current practice, federal agencies purchase our most sensitive and personal information scraped from apps and sold by third-party data brokers. The general counsels of intelligence and law enforcement agencies assert a right to see our most personal information without the need to get a warrant, in flagrant disregard of the Fourth Amendment to the Constitution.” “This is the kind of practice one expects of a surveillance state, not America.” The House now officially agrees. This measure would require agencies within the Department of Defense to get a probable cause warrant, court order or subpoena to purchase personal information that in other circumstances would require such a warrant. “This amendment strikes a reasonable balance between respecting the privacy of Americans while leaving the government with the power to search for potential threats to the homeland,” says Bob Goodlatte, PPSA Senior Policy Advisor. “The Senate should respect the groundswell of bipartisan support shown in the House today for this amendment in the NDAA.” In today’s House Committee Judiciary hearing with FBI Director Christopher Wray, Rep. Pramila Jayapal (D-WA) expertly revealed the extent to which the FBI is unwilling to publicly discuss its use of commercially available information (go to 1:10:50 mark).
Rep. Jayapal asked the director about his claim before the Senate Intelligence Committee in March that the FBI had previously purchased Americans’ location data information from internet advertisers but had stopped the practice. Why, then, Jayapal asked, did a report from the Office of the Director of National Intelligence (ODNI) reveal that the government continues to purchase Americans’ personal data scraped from apps and sold to the government by third-party data brokers? The report was surprising for its frankness. An ODNI panel admitted that such data can be used to “facilitate blackmail, stalking, harassment, and public shaming.” Rep. Jayapal asked how the FBI uses such data. Director Wray responded that this is too complex to cover in a short exchange. He said there are so many precise definitions that he had best send “subject matter experts” from the FBI to give Rep. Jayapal a briefing, presumably behind closed doors and under classified rules that would prevent public discussion. Rep. Jayapal then went on to note that more than historic location data is at stake. Purchased data, she said, include biometric data, medical and mental health records, personal communications, and internet search histories and activities. She asked Director Wray: Does the FBI have a written policy on how it uses such commercially available information? Director Wray did not seem sure. He replied that he would be happy to provide a private briefing. Rep. Jayapal next asked if there is an FBI policy for using purchased information against Americans in criminal cases. Once again, Director Wray punted. After Rep. Jayapal was finished, House Judiciary Chair Jim Jordan (R-OH), said that her remarks were “well said,” and promised a bipartisan approach on the issue. Speaking for Republicans, Chairman Jordan told Rep. Jayapal, chair of the progressive caucus, “you have friends over here who want to help you with that.” We suggest that a bipartisan next step could be an open hearing with the FBI’s experts on how much purchased information is obtained and how it is used. Technology presents new challenges in the protection of Fourth Amendment rights, especially regarding expectations of privacy and warrantless searches. A key question, as the U.S. Supreme Court found in 2001, is how to preserve “that degree of privacy against government that existed when the Fourth Amendment was adopted.”
A recent case out of Maryland goes a long way in enshrining critical protections for personal data in that state, striking a bold contrast with other recent decisions that degrade privacy. The Fourth Amendment to the United States Constitution guarantees the “right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures…” [emphasis added] Since the advent of the digital age, courts around the country have analogized personal data to the founding-era concept of personal papers, which the Supreme Court has long held to be safeguarded against unwanted intrusion. Yet, the Court has gone further in recent years, finding that digital information implicates “privacy concerns far beyond those implicated by the search of a cigarette pack, a wallet, or a purse.” After all, any thorough search of a citizen’s digital data is bound to turn up troves of personal information – from banking information to private correspondence – unrelated to the particularities of a warrant. It makes sense that our digital footprints would merit enhanced protection. Despite this seeming clarity, much ambiguity persists surrounding the protection of digital data. State of Maryland v. Daniel Ashley McDonnell presents a novel question of law and fact unresolved at the national level: Does a reasonable expectation of privacy exist in the contents of a copied computer hard drive after consent to search that hard drive has been revoked? The Supreme Court of Maryland found that it does. Here’s the background: Daniel Ashley McDonnell granted investigating officers’ consent to search his computer. Police subsequently made a forensic copy of McDonnell’s hard drive and proceeded to analyze its data even after McDonnell withdrew his consent. For its part, the state argued that McDonnell lost any reasonable expectation of privacy once he allowed his data to be copied. In constitutional law, warrantless searches of person or property are considered unreasonable unless certain exceptions apply – if a person lacks any reasonable expectation of privacy, for example, or if consent is granted to perform a search. Generally, when that consent is revoked, authorities may not conduct a search by relying on the prior consent. In this case, the Supreme Court of Maryland found that McDonnell had a privacy interest in his data itself – not in the hard drive copy made by investigating authorities. Had the police examined the hard drive data while consent was in effect, McDonnell would have lost any reasonable expectation of privacy in that data. But given that consent was withdrawn prior to the search, he maintained that expectation absent an independent search justification. The court wrote: “To accept the State’s stance--i.e., that Mr. McDonnell irrevocably lost all privacy interest in the data on his hard drive when he allowed [police] to copy it—would be to permit a limitless search through vast quantities and a varied array of personal data that the Supreme Court of the United States has characterized as consisting of more information than would be found in an exhaustive search of a person’s home.” In a similar case, the U.S. District Court for the Middle District of Florida came to a different conclusion, finding that “revocation of consent does not require the suppression of evidence already lawfully obtained.” However, the preponderance of case law and legal scholarship suggests the Supreme Court of Maryland struck the right balance. Its opinion is consistent with recent scholarship by law professor Orin Kerr, who argues that “the same Fourth Amendment rules that apply to searching a suspect’s computer should also apply to searching the government’s copy.” It is further consistent with the U.S. Supreme Court’s warnings in Riley v. California, which noted the potential of a cell phone search to reveal “[t]he sum of an individual’s private life.” The Supreme Court of Maryland’s decision is a win for data privacy. To quote the amicus brief from our friends at Restore the Fourth, absent such protections the government could “copy and indefinitely detain every private paper on a person’s hard drive (i.e., millions of documents) at minimal cost—except to the Fourth Amendment.” The Maryland decision was well reasoned and well done. ACLU is celebrating the 15th anniversary of the Foreign Intelligence Surveillance Act (FISA) amendments by highlighting a floor statement President Joe Biden made as a U.S. Senator in 2008.
In his Congressional Record submission, Sen. Biden declared the measure that we would come to know as Section 702 as “constitutionally infirm.” He voted against it. Sen. Biden’s words would be a better guide to President Biden’s surveillance policies than those advocated by his appointees and representatives today. For months now, the administration’s representatives on Capitol Hill have argued that Section 702 of FISA should be reauthorized without changes or reforms. FBI Director Christopher Wray and others have, with the backing of the president, made this case even though, by the administration’s own admission, this authority meant by Congress to authorize surveillance of foreigners located abroad has been used in 246,000 targeted searches of Americans’ communications. While we should not uncritically accept the government’s numbers, and the definitions and assurances behind it, let’s take the government’s number as a minimum. The question remains why the government believes 246,000 violations of Americans’ civil liberties is acceptable. That number constitutes millions of civil rights violations in a few years and more violations than there are people in a sizable city, say, Richmond, Virginia. As a U.S. Senator, Joe Biden foresaw problems with Section 702. He complained that the law authorized only weak judicial oversight by the FISA Court, beholden to the good faith of executive branch officials. Sen. Biden said the Attorney General and the Director of National Intelligence would certify after the fact to the FISA court that they had good reason to believe targets were located outside of the United States, “regardless of how many calls to innocent American citizens inside the United States were intercepted in the process.” “This would be a breathtaking and unconstitutional expansion of the President’s powers,” Sen. Biden said. Now those powers are in the hands of President Joe Biden. As senator, Joe Biden set out an overarching principle we’d all be wise to remember: “One of the defining challenges of our age is to combat international terrorism while maintaining our national values and our commitment to the rule of law and individual rights. These two obligations are not mutually exclusive. Indeed, they reinforce each other.” PPSA has been hearing as much from Congressional leaders, from Democrats as well as Republicans. Our point is not to slam Joe Biden for inconsistency, but to sharpen the debate for Members of Congress. The president was right the first time: We can have protection from terrorists and spies without jettisoning our civil rights. We can reform Section 702 so it will work within the guardrails of the Constitution. Sens. Ron Wyden and Rand Paul are renewing their push for the Protecting Data at the Border Act, a bill to ensure that government agents, including agents of Customs and Border Protection, obtain a warrant to search the personal data of Americans returning from abroad. The measure would send a resolute message: Americans' digital privacy is guaranteed, even at the border.
Until 2014, the federal government claimed it did not need a warrant to search a device if a person had been arrested. In Riley v. California, a landmark Supreme Court case, the Justices unanimously held that the warrantless, deep search of the digital contents of a cell phone during an arrest is unconstitutional under the Fourth Amendment. If this principle pertains to an arrestee, how much more should it pertain to an American citizen who is merely traveling? Yet border zones, whether points of entry to Canada or Mexico, or airports, have become legal twilight zones where the Fourth Amendment is treated as a suggestion. With ever-increasing international traffic, the potential for government misconduct grows as well. PPSA has called attention to constitutional loopholes at the border before. In 2021, we reported that two troubling trends at the border threatened the rights of Americans. One is the rollout of facial recognition technology and other biometric surveillance by Customs and Border Patrol, which is used on citizens and non-citizens who arrive at a U.S. airport. The other – and by far the most intrusive – is the existing practice of accessing the contents of returning citizens’ cellphones, laptops, and other electronic devices. In 2017, a NASA employee was stopped by Customs and Border Patrol agents and told he could not leave until he gave CBP agents his password to his phone, which belonged to NASA and contained sensitive and confidential information. In an ACLU petition filed to the Supreme Court in 2021 (Merchant v. Mayorkas), eleven U.S. citizens sued over having their electronic devices examined at the border without a warrant or reasonable suspicion. Unfortunately, the Court declined to hear the case. PPSA endorses the Protecting Data at the Border Act. This bill will go a long way towards codifying and ensuring that the Fourth Amendment protects American citizens at the border. The bill will also prohibit officials from delaying or denying entry to the U.S. if a person declines to hand over devices and requires law enforcement to have probable cause to seize a device. Bob Goodlatte, PPSA senior policy advisor and former Chairman of the House Judiciary Committee, said: “There is no excuse for the government to suspend the Fourth Amendment at the border. While it is reasonable for border agents to protect the nation with inspections for pests, contraband, and illegal narcotics, it is an outrageous violation of the Constitution for agents to scan the contents of our digital devices, delving into the sensitive and personal aspects of our domestic lives. “Sens. Ron Wyden and Rand Paul are stepping up to remind the government that we don’t shed our constitutional rights just because we travel.” The intelligence community and FBI are strenuously lobbying Congress that Section 702 of the Foreign Intelligence Surveillance Act, set to expire at the end of this year, should get a “clean” reauthorization – without any amendments or reforms.
Some Members of Congress are dead set against any reauthorization of Section 702, an authority designed by Congress to allow the surveillance of foreigners on foreign soil but has been used by government agencies – the FBI most notably – to spy on Americans at home. Sen. Lindsey Graham (R-SC) sounded a note of caution to both sides in this debate. He recently noted that if Congress fails to reauthorize Section 702, “the country will be much at risk” without an ability to identify “some pretty bad actors.” “The ISIS Al Qaeda footprint is coming back, China’s up to no good at every front, the Iranians are threatening to kill members of the Trump Administration and many of us have been briefed by the FBI based on pick-ups you’ve had regarding threats against us,” Sen. Graham said. But the senator pushed back on the notion that 702 should be reauthorized without needed reforms. “The downside is it has been abused and there’s a warrant requirement to investigate an American citizen for potential wrongdoing,” Sen. Graham said, “And we don’t want this to be used to get around a warrant requirement, so the bottom line is let’s reauthorize this program and build in some safeguards.” It’s well and good that more leaders on the Hill are seeing the need for reform. PPSA looks forward to seeing Sen. Graham and his colleagues follow through on their recognition that new safeguards are needed. Beneath the surface of Russia’s ever-changing autocratic regimes has always been suppressed but vibrant conversations in samizdat, private media in the form of homemade newsletters and clandestine literature. In the era of Putin and the Ukraine war, discussion among dissenters and dissidents is facilitated by end-to-end encrypted technologies such as Signal, Telegram, and WhatsApp. In a recent article in The New York Times, Aaron Krolik, Paul Mozur, and Adam Satariano call attention to Russia’s successful infiltration of these platforms to effectively eliminate dissent.
This trend promises devastating consequences for Russian dissidents and danger for the world. The Russian government has managed to crack these once-secure channels, leveraging them to map networks of relationships and surveil its citizens. This alarming development is transforming Russia into a full-blown surveillance state like China’s, where private conversations are no longer secure and individuals risk persecution for expressing dissenting views. Even more concerning is the certainty that new surveillance technologies and techniques will be easily exported to unfriendly countries and illicit groups around the world, much like Israeli-made Pegasus has been. The ability of Pegasus to infiltrate mobile devices and monitor individuals has been employed by various governments and threat actors worldwide, undermining privacy and individual freedoms. New Russian spyware provides a similar “Swiss-army knife of spying possibilities,” enabling an unprecedented degree of surveillance and intrusion. One program can identify when people make voice calls or send files on encrypted chat apps such as Telegram, Signal, and WhatsApp. The software can map a person’s relationship network by tracking communications with others. Another product can collect passwords entered on unencrypted websites. Another tool can map the locations of two phones over the course of the day to determine whether they met, indicating a potential meeting between people. Russia is effectively building a surveillance industrial complex, one which it plans to sell around the world. According to the U.S. State Department, one Russian surveillance company, Citadel, already controls between 60 to 80 percent of the global market for telecommunications monitoring technology. “The spillover effects will be felt first in the surrounding region, then potentially the world,” says Adrian Shahbaz, Vice-President of research and analysis at the pro-democracy advocacy group Freedom House. In the hands of a much larger and more sophisticated rival, like China, these tools can be a force for global repression. China has already developed the most robust facial recognition surveillance system in the world, which will integrate voiceprints, faceprints, and DNA samples to weave a comprehensive portrait of the individuals who make up its huge population. China can infiltrate cell phones and sweep up location data from many phones in a wide area. It is even developing the ability to observe brainwaves to detect what illegal activities residents might be up to. Technologies such as these are not likely to remain contained just to China or Russia. Pegasus shows how such technology can be used to menacing effect. Pegasus was deployed against 26 Mexican journalists in 2016 and 2017. At least one was assassinated. Saudi Arabia successfully installed Pegasus on the phone of the wife of murdered dissident Jamal Khashoggi. Pegasus has even been found on the phones of several U.S. policymakers and in the office of the British Prime Minister. You may not be worried that the Russian government has its eyes on you, but these capabilities will be sold to unfriendly forces around the world. A cartel could use these technologies to target Americans. An unscrupulous corporation could use them to develop an even more intricate and suggestive profile of potential customers. A government, perhaps our own, could use them to counter freedom of speech. This is all the more reason for Americans to protect personal encryption from U.S. government pressure to provide backdoor access, while urging private sector champions to stay in the race with the tyrants. “Fruit of a Poisonous Tree”FBI documents acquired through Freedom of Information Act (FOIA) requests by PPSA and the American Civil Liberties Union show how authorities continue to conceal information about how stingray technology is really being used. The downstream effect of this deception likely results in defendants being denied the ability to know how a case was constructed against them, degrading their right to a fair trial.
Dozens of federal and state agencies have benefitted from the generosity of the Department of Justice in sharing with state and local police cell-site simulators, popularly known by the brand name “Stingrays.” These devices trick cellphones into revealing their owners’ locations and other sensitive, personal information. An email from the Bureau of Alcohol, Tobacco, Firearms and Explosives (ATF), released today by PPSA, one ATF official writes to another: “To remain consistent with our DOJ Partner, in this case, the USMS (U.S. Marshall Service) since they are the largest user of this technology, we respectfully request that this technique not be disclosed in an affidavit.” ACLU’s FOIA shows the same instructions from the federal government imposed in nondisclosure agreements on police departments when they ask for this technology to track suspects. These contracts don’t beat around the bush. They explicitly require police departments to withhold information about stingrays and their usage from defendants and lawyers. The FBI argues that such secrecy is required to prevent revealing information that would enable criminals to “thwart law enforcement efforts.” But what’s the big secret? Despite the clandestine nature of this federal/local partnership program, stingray technology and its capabilities have been an open secret for years now. This technology was depicted under another brand name – “triggerfish” –on season three of HBO’s The Wire. That was in 2004. Could the real secret be that police departments are conspiring with the FBI to conceal the use of privacy-invading technology to give prosecutors an unfair, “backdoor” advantage in their cases? PPSA has often reported the ways in which federal or state agencies routinely circumvent constitutional privacy protections. One well-known method is the parallel construction of evidence, in which prosecutors leverage illicitly gained knowledge to turn up evidence from a source acceptable in court. It is well established legal doctrine that illicit evidence, the “fruit of the poisonous tree,” should not be admissible. But who knows what is poisonous if the tree is hidden? The acquired federal documents actually spell out how parallel construction should work – advising the police to pursue “additional and independent investigative means and methods” to obtain evidence collected through use of a cell-site simulator. The suggestions on how to accomplish such secrecy were redacted by the FBI. The Bureau argues that revealing information about stingrays would have a “significant detrimental impact on the national security of the United States.” The revelation of even minor details is so heavily restricted that police have dropped charges against a suspect rather than unveil information in open court. “The important question posed by privacy advocates is why are police departments and the FBI going to such lengths to conceal information about a technology that is public knowledge?” asked Bob Goodlatte, former chairman of the House Judiciary Committee and PPSA Senior Policy Advisor. “The capabilities of stingrays are well-known, with knowledge of their deployment on popular television almost twenty years ago. “Yet the government still insists that the basics of stingray use is a precious national secret,” Goodlatte said. “Congress should demand to know if there is any basis at all for these non-disclosure agreements – and how common parallel construction really is in practice.” The digital trail you leave behind can be used to create a profile of you by your race, religion, gender, sexual orientation, financial issues, personal medical history, mental health, and your physical location.
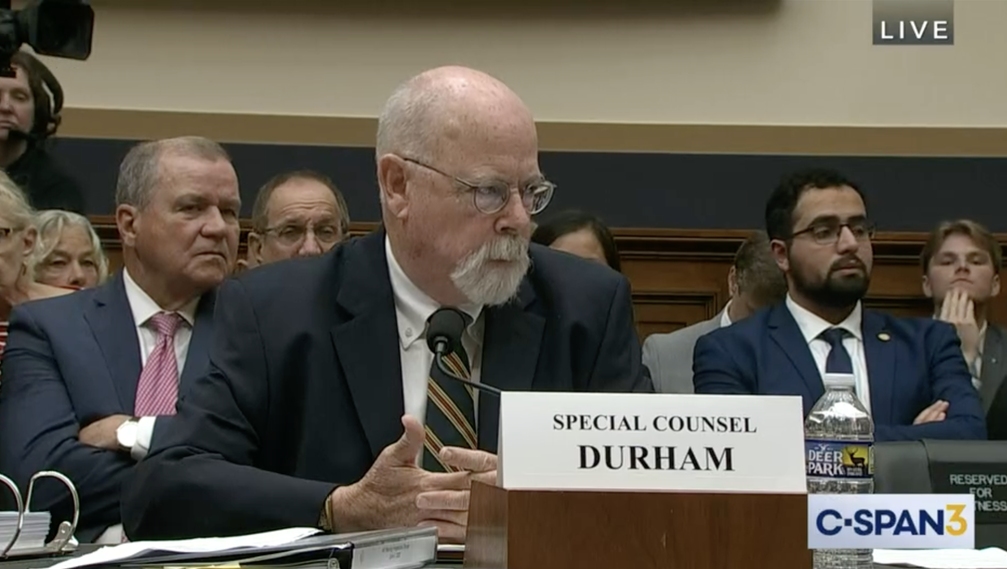
PPSA has long warned against the routine sale of our personal and sensitive information scraped from apps and sold to U.S. federal agencies by data brokers. The general counsels of these law enforcement and intelligence agencies claim that they are not violating the Fourth Amendment prohibition against warrantless search and seizure because they are not seizing our data at all. They’re just buying it. That is galling enough, but what about hostile governments accessing your most personal information? They have no guardrails and would surely have no scruples in using your information against you and, for those in the military or other sensitive positions, the United States. Under Chinese law, China’s technology companies are obligated to share their data with Chinese intelligence. Imagine all the data Chinese military, intelligence, and commercial actors have on the 80 million American users of TikTok. Then multiply that by all the data China acquires through legal, commercial means. “Massive pools of Americans’ sensitive information – everything from where we go, to what we buy and what kind of health care services we receive – are for sale to buyers in China, Russia and nearly anyone with a credit card,” said Sen. Ron Wyden, (D-OR), sponsor of the Protecting Americans’ Data from Foreign Surveillance Act of 2023. “The privacy and security of our data is essential to the freedoms we hold dear,” said co-sponsor Sen. Cynthia Lummis (R-WY). “If foreign adversaries can access our data, they can control it.” Their bill is also supported in the Senate by Sens. Sheldon Whitehouse (D-RI), Bill Hagerty (R-TN), Martin Heinrich (D-NM), and Marco Rubio (R-FL). It is supported in the House by Rep. Warren Davidson (R-OH) and Rep. Anna Eshoo (D-CA). This bill would apply tough criminal and civil penalties to prevent employees of foreign corporations like TikTok from accessing U.S. data from abroad. “Freedom surrendered is rarely reclaimed,” said Rep. Davidson. PPSA agrees and supports this bill. “The need to address foreign exploitation of Americans’ data is urgent,” said Bob Goodlatte, former House Judiciary Committee Chairman and Senior Policy Advisor to PPSA. “This legislation should also prompt us to get our own house in order. Members should address exploitation of our personal information by our government. I hope every member who signs on to this bill supports requiring the U.S. government to obtain a warrant when it wishes to inspect our commercially acquired information, as well as data from Section 702 of the Foreign Intelligence Surveillance Act.” The substance of Special Prosecutor John Durham’s appearance earlier this week before the House Permanent Select Committee on Intelligence (HPSCI) is not public. But it is clear from the attitudes of Members who emerged from that closed hearing that what they heard – and discussed – left them with a determination to insist on reform of Section 702 of the Foreign Intelligence Surveillance (FISA) as a condition for renewing this surveillance authority in December.
Durham’s famous report on the FBI/Carter Page surveillance scandal centered around FISA’s Title 1 authority, which involved repeated submissions by the FBI to surveil Trump campaign aid Page. With lies of omission and commission, these submissions included a forged document by an FBI lawyer that attempted to hide Page’s service to the CIA as a highly rated informant. Rep. Mike Turner, committee chairman, and Rep. Jim Himes, ranking member, both agreed that Durham’s appearance before the committee without cameras led to a probing and dispassionate discussion that included ways to reform Section 702 of the Foreign Intelligence Surveillance Act (FISA). “It was interesting to hear from Mr. Durham that he has concerns that there are reforms that need to go in place, and that there are still issues that need to be addressed,” Chairman Turner said. “I think that we were able to get some information that would be very helpful for us and the work that we have to do on both FISA renewal, FISA reforms, and also reform issues with the FBI.” Ranking Member Himes also came out of that HPSCI hearing saying that there was a near-unanimous view on the committee that 702 has to be “reauthorized with reforms.” It is easy to connect the dots. If Members heard how easily the FBI could misinform a FISA court judge, how much easier would it be to jump any guardrails when Americans’ personal data is examined under the 702 process, which is not under any judicial review? And it is likely the hearing unscored for Members that even when there is a federal judge, whenever there is a case in which sensitive First Amendment rights of Americans are at stake – as in the obvious case of a presidential campaign – the appointment of a civil liberties expert as an advisor to the court, or amicus, should be required. Just imagine how much trouble might have been avoided for the nation, a presidential campaign, and the FBI itself if the bureau had been simply forced to answer tough questions before FISA court Judge James Boasberg. In 2018, the U.S. Supreme Court held that a warrant is needed before government agencies can seize your location history from cell-site records. That opinion, Carpenter v. United States, often described as a landmark ruling, has actually become little more than a legal watermark thanks to the machinations of government agencies.
When a government agency wants to know where you’ve been, or anything about you, all it has to do is consult the trove of sensitive personal information on millions of Americans scraped from apps and purchased from third-party data brokers. No warrants required. As they used to say in internet ads, the government knows all about you with this one weird trick. Two responses to PPSA Freedom of Information Act (FOIA) requests show how freely the FBI and DIA access Americans’ personal information. The FBI has a team dedicated to working with cell tower data. Their specialties include “historical CDR (call detail records) analysis and geospatial mapping,” which enables the tracking of people across multiple towers. The FBI conducts “tower dump analysis,” which seems to be the collection of bulk data from cell towers and “real-time cellular tracking” services. The documents obtained by PPSA show that the FBI regularly lends out these services to state and local governments. The Defense Intelligence Agency documents show that the agency uses commercially available data for “cover operations.” Does this mean DIA is using data to help agents impersonate real people? Or is DIA using our personal information as material from which to create fake, chimeric identities, using a blend of personal information from multiple real people? These are just glimpses into how the government uses our personal information, from our movements to our personal interests, relationships, and beliefs. PPSA will continue to use FOIAs and lawsuits to dig out more details about these practices. PPSA today announces the submittal of a Freedom of Information Act (FOIA) request with the Department of Justice seeking records on how and when DOJ uses secretive non-disclosure orders, or NDOs. Through such orders, DOJ is able to obtain private information from internet and telecom companies while also prohibiting those companies from informing American consumers that their personal information has been searched by the government.
In June, the House passed the NDO Fairness Act by voice vote. If enacted, this legislation would restrain the government practice of issuing NDOs to internet and telecom companies. While the Senate prepares to take up this legislation, PPSA thought it would be useful to inform the debate with information on the circumstances and frequency with which the Department of Justice and its agencies issue NDOs. We also thought it would be useful for senators to know what privacy safeguards are in place, including government guidelines, policies, and training requirements. With that in mind, PPSA submitted this FOIA request to the Department of Justice, and its components – the Executive Office for United States Attorneys, the FBI, the Drug Enforcement Administration, DOJ’s Criminal Division, and the Bureau of Alcohol, Tobacco, Firearms and Explosives. We are asking for records concerning:
“We have every reason to expect the government can release this basic data about how many NDOs are issued, the circumstances that prompted them, and the guardrails, if any, that constrain them,” said Gene Schaerr, PPSA general counsel. “We are not asking the government for a favor. We are seeking information Americans should know and the Senate needs for its debate.” PPSA today announced the filing of a Freedom of Information Act (FOIA) request with the Department of Justice asking for documents and records showing whether DOJ ensures it has probable cause before issuing administrative subpoenas to seize Americans’ private electronic data.
Civil libertarians have long suspected that the DOJ often uses such administrative subpoenas to circumvent the probable-cause requirement for searching Americans’ records. This is particularly troubling, since such subpoenas, issued without a court order or judicial oversight, are often used to collect bulk data rather than targeting information from an identifiable target. “It may be likened to a fishing expedition, with Americans as the fish,” said Gene Schaerr, PPSA general counsel. PPSA’s FOIA request covers all the components of the Department of Justice, including the Executive Office for United States Attorneys, the FBI, the Drug Enforcement Administration, the DOJ’s Criminal Division, and the Bureau of Alcohol, Tobacco, Firearms and Explosives. PPSA is seeking:
“We are not asking about sources or methods or anything else that would trigger a Glomar response that would shut off all disclosure,” Schaerr said. “We seek topline information necessary for Congress to conduct oversight and for the American people to understand how our government uses our most personal and sensitive information.” FBI Director Christopher Wray and senior leaders of other federal law enforcement and intelligence agencies are encountering stiff, bipartisan headwinds as they make the rounds on Capitol Hill to secure reauthorization of Section 702 of the Foreign Intelligence Surveillance Act without changes. A new poll from the Associated Press-NORC Center for Public Affairs of adults across the country shows that Members of Congress are just being sensitive to the strong views of their constituents.
Historically, Republicans have been more security conscious and more likely to sacrifice some level of freedom for enhanced safety. Democrats were much more likely to put protection of civil liberties first. The AP-NORC poll shows that after a series of federal surveillance scandals and revelations, respondents from both parties have similar views. The most prominent trend is that public opposition to warrantless surveillance has dramatically increased over time.
The bottom line for surveillance hawks wearing out the soles of their shoes walking the House and Senate office buildings is that only 28 percent of Americans support warrantless spying on communications outside of the United States. That alone should tell them that Section 702 is not going to be reauthorized without significant reforms. The growth of anti-surveillance skepticism has been especially pronounced among Republicans. In 2011, 69 percent of Republicans said it is sometimes necessary to sacrifice rights and freedoms to prevent terroristic threats to the homeland. Today, that number is down to 44 percent. Today, a majority say it is never necessary to sacrifice rights and freedoms to fight terrorism. For all the focus on digital privacy, traditional Fourth Amendment violations by the government are as common as ever. One area of habitual constitutional overreach is child welfare, as illustrated by a recent, disturbing event in Waltham, Massachusetts.
In the early morning hours of July 16, 2022, officials from the Massachusetts Department of Children and Families, flanked by several armed police officers, knocked on the door of Waltham residents Sarah Perkins and Joshua Sabey and demanded the surrender of their children. The officials had no warrant. There were no exigent circumstances. They had no reason to believe the children were in imminent threat of bodily harm. Yet, despite the parents’ reasonable protestations, the officers issued an ultimatum: Give us your children or we’ll break down the door and take them. Ultimately, Sarah and Josh gave in to the inevitable, ushering their sobbing children into the waiting cars of strangers, who whisked them away in the night. Nationally, more than three million children come under the care of state child protective services each year. In cases involving home searches, according to a recent study by ProPublica, authorities rarely – if ever – obtain a warrant. In New York, for example, research shows that the Administration for Children’s Services obtained a warrant or entry order in less than 0.2% of instances. The Fourth Amendment plainly states: “The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated.” (The founders never thought it was necessary to also add, “and their children!”) That amendment requires a probable cause warrant to examine a home. Constitutional protections extend to the states through the Due Process Clause of the Fourteenth Amendment, yet child welfare agencies largely operate as though exempt from such constitutional strictures, regularly entering homes based on vague determinations of imminent threat to a child. Let us be clear: such concerns are often well founded, and we support the right of the state to intervene to protect abused or neglected children. But there needs to be a lawful process. The case of Sarah Perkins and Joshua Sabey is an instructive example of what can happen when there are no guardrails on the discretionary exercise of police power. These parents fell under the suspicion of child welfare authorities after taking their three-month-old to the hospital for high fever. When staff members conducted an X-ray, they discovered a healing rib fracture. Concerned about abuse, they called in a social worker who questioned Sarah about the injury. For her part, Sarah had no clue how the injury occurred, though it was later determined that the child’s grandmother may have inadvertently caused it while removing the child from a car seat. For three days, the parents were subjected to a thorough investigation, which included home visits and persistent interference by state authorities, who found neither evidence of abuse nor danger in the home. Everything seemed fine until three days later, when a DCF supervisor made the seemingly arbitrary decision that the children should be taken into custody in the middle of the night. Sarah and Joshua were eventually cleared of any misconduct and re-acquired full custody following several months of legal wrangling. But what about families that lack the resources to engage in such a prolonged fight? The application of the Fourth Amendment to child protective services is an area that requires sharper legal definition. A circuit split exists on the issue and the Supreme Court has not specifically weighed in. Sarah and Josh, meanwhile, have rightly filed suit against individuals at DCF and the Waltham Police Department alleging unreasonable search and seizure and due process violations under the Fourth and Fourteenth Amendment, respectively. They’re also working with members of the Massachusetts legislature on a new law that would require approval by an on-call judge before any after-hours removal. It’s a reasonable constraint on the currently unchecked power of a vast, often adversarial government bureaucracy. There is no question that real and heartbreaking instances of child abuse occur. Child protective services must have the power to remove children from these circumstances. But such power must not be limitless. Of all our constitutional and natural rights, parental rights are the most precious. Admits Potential for Abuse of Government Spying into Americans’ Politics, Religion, and Sex Lives For years, PPSA has warned about the vast amounts of sensitive personal information about our private lives that are scraped from our apps and sold by third-party data brokers to government intelligence and law enforcement agencies. Now we have telling details from the inside.
On Friday, the Office of the Director of National Intelligence released a declassified report from a senior advisory group that sheds new light on the dangers posed by Commercially Available Information (CAI). Unlike most government documents, this report is remarkably self-aware and willing to explore the dangers of this policy in plain language. This panel details all the many sorts of data that the government collects about us from commercial sources.
One data broker with the exceptionally creepy name of PeekYou brags that it “collects and combines scattered content from social sites, news sources, homepages, and blog platforms to present comprehensive online identities.” The panel is forthright about how this data can be used to “facilitate blackmail, stalking, harassment, and public shaming.” It is not difficult, the report notes, for deanonymized information (which exposes a person’s identity) sold by data brokers to be combined or used with other data “to reverse engineer identities or deanonymize various forms of information.” The authors of this report recognize how dangerous it is for the intelligence community to have this much commercially available information on its citizenry at its fingertips. “The government would never have been permitted to compel billions of people to carry location tracking devices on their persons at all times, to log and track most of their social interactions, or to keep flawless records of all their reading habits. Yet smartphones, connected cars, web tracking technologies, the Internet of Things, and other innovations have had their effect without government participation. While the IC cannot willingly blind itself to this information, it must appreciate how unfettered access to CAI increases its power in ways that may exceed our constitutional traditions or other societal expectations.” The authors note that “CAI could be used, for example, to identify every person who attended a protest or rally based on their smartphone location or ad-tracking records.” And the danger to the American people is not just from our government: this report warns of “intelligence benefits to our adversaries,” allowing foreign agencies to use open-source intelligence and AI to disinform and influence the public. It cites a chilling factoid from a Duke University report that of the 10 major data brokers, three advertise an ability to provide data to identify U.S. military personnel. The ODNI report quotes the Duke study that foreign actors could use CAI “to bolster their influence campaigns to interfere in U.S. electoral processes. Criminal organizations could use this data to build profiles on and subsequently target prosecutors and judges. Foreign intelligence organizations could acquire this data through a variety of means – including through front companies that could legally purchase the data from U.S. brokers and through simply hacking a data broker and stealing it all – to build profiles on politicians, media figures, diplomats, civil servants, and even suspected or secretly identified intelligence operatives.” The authors recognize a danger for U.S. agencies, that “mission creep” can “subject CAI collected for one purpose to other purposes that might raise risks beyond those originally calculated.” It raises the question of the government’s obligation to respect the Fourth Amendment in accessing technologies that track our movements. It highlights the principles set out in a Supreme Court opinion that requires a warrant for certain kinds of cellsite location data. Yet the report notes that the Defense Intelligence Agency nevertheless provides funding to “another agency” for it to purchase commercially available geolocation data aggregated from smartphones. The author admits it is unclear whether this data is for U.S. locations or foreign ones. The report says that agencies rely on a facial recognition company, Clear, not only to “resolve identities,” but also to locate people. The authors challenge the bland assertions of federal agencies that Commercially Acquired Information, CAI, is the same as Publicly Available Information, PAI. “In our view, profound changes in the scope and sensitivity of CAI have overtaken traditional understandings, at least as a matter of policy. Today’s publicly available CAI is very different in degree and in kind from traditional PAI.” The authors refer to Riley v. California, a Supreme Court case that required a warrant before police could access information in a suspect’s cellphone. The report quotes the Court that asserting that modern CAI is materially indistinguishable from traditional PAI “is like saying a ride on horseback is materially indistinguishable from a flight to the moon.” Having defined the problems, the authors of this report advance possible solutions. They propose internal processes that could minimize the dangers of mass collection of our private information, changes in how information is cataloged, developing standards and procedures, heightening approvals for information in “sensitive” categories, the creation of additional mitigation measures, and developing more “precise sensitivity and privacy-protecting guidance for PAI.” The authors of this report should be commended for their frankness. Their solution, however, would merely replicate the failed approach of the FBI in its repeated attempts to reform the processes used to extract Americans’ personal information from Section 702 of the Foreign Intelligence Surveillance Act. In both instances, the answer to these dilemmas is the Fourth Amendment’s probable cause warrant, an 18th century solution for these 21st century dilemmas. Sen. Ossoff Pins Down FBI: Why Not Warrants? When the Senate Judiciary Committee announced it was holding a hearing this morning on Section 702 of the Foreign Intelligence Surveillance Act with five men representing the Office of the Director of National Intelligence, the NSA, CIA, FBI, and the Department of Justice, many assumed it would amount to a bit of surveillance state agitprop.
Instead, senators from across the aisle grilled these intelligence community deputy directors and general counsel like so many hot dogs. The intelligence community representatives came lined up with talking points about a new “culture of compliance” in the intelligence community, only to be upended. Compliance with what? The law? The Constitution? No, the answer consistently was compliance with updated, byzantine internal regulations that this time – they swear! – will finally protect the constitutional rights of the American people. Sen. Mike Lee (R-UT) burst out like a rodeo bull to lecture the panelists that the government has shown “shocking disregard for Americans’ constitutional rights and civil liberties,” from illegal surveillance of political donors, protestors, and even a sitting Member of Congress. He expressed frustration from years of hearing from FBI directors and attorneys general under three presidents say, “just trust us, don’t worry, we’ve got good people … and lots and lots of procedural safeguards in place.” Sen. Lee ridiculed the FBI’s boast that it has vastly reduced the hundreds of thousands of spying incidents without a probable cause warrant. (Go to 1:37:51 mark) Sen. Lee said: “The number should not just be going down. That number should be zero. Every ‘non-complaint’ search violates an American’s constitutional rights.” Sen. Jon Ossoff (D-GA), who sits on both the Judiciary and Intelligence committees, was cool and unflappable as he brushed aside Assistant Attorney General Matt Olsen’s attempts to bat away his questions (go to 1:58:35). Sen. Ossoff drilled down on the need for a probable cause warrant in using “U.S. person communications” – when the FBI is looking at domestic crimes in the Section 702 database. “Section 702 is a foreign intelligence tool, it is not a law enforcement tool,” Olsen said. “So why is it used for domestic law enforcement purposes?” Sen. Ossoff asked. Olsen replied that such “crime only” searches are “exceedingly” rare. “If it is as rare as you state,” Sen. Ossoff said, “why not go get a warrant?” Olsen then told a story of an agent looking into Section 702 information on national security grounds only to find evidence of domestic child abuse. Sen. Ossoff recognized this as an attempt at obfuscation. “We’re talking about seeking evidence of a crime only, we’re not talking about encountering evidence of other crimes in the course of querying foreign intelligence information,” Sen. Ossoff said. “We’re talking about U.S. person queries whose sole purpose is investigating domestic crime. Why should that not require a warrant?” Olsen’s reply was a legal tautology. Section 702 data, he said, is “lawfully collected information that is in the FBI’s holdings.” “I don’t think you’ve made the case,” Sen. Ossoff said, again noting the FBI uses Section 702 for many purely domestic crimes. In his calm but persistent questioning, Sen. Ossoff revealed the deeper issue of how the FBI gets around the law by using a foreign surveillance authority to set up backdoor searches to target Americans in domestic cases. Sen. Dick Durbin (R-Il), committee chairman, had set the tone by asking why improper searches of Americans’ communications were conducted some 278,000 times in a recent one-year period. Chairman Durbin noted that 19,000 searches of a federal candidate’s donors were queried when, in fact, only 8 targeted donors showed a connection to foreign intelligence. Sen. Lindsey Graham asked how we can be sure FBI agents using Section 702 are “not being lazy, not getting around the law?” Olsen replied that one person in the Department of Justice was fired for misusing Section 702 and that the FBI now has a “three-strikes” policy regarding 702 violation. That seemed to win little gratitude from senators. Overall, the tone of this hearing was frank, harsh, and unrelenting. These five men may have started their day believing that their assurances, and 11th hour proposals to further reform the government’s internal processes, would ensure smooth sailing. Afterwards, these intelligence community representatives should return to the leaders of their respective agencies and tell them: “We’ve either got to accept serious reform of Section 702 or wave it goodbye.” Four Surveillance Experts Explain Ever wonder why Congress doesn’t do a better job of oversight of the intelligence community and its vast, unaccountable surveillance system that spies on us?
The answer, says Bob Goodlatte, former chairman of the House Judiciary Committee and PPSA Senior Policy Advisor, is that the security clearances held by Members are meaningless if the executive branch restricts what they are allowed to see. And some Members have become too close to the agencies they are tasked with overseeing to do their job objectively. Another factor in weakening Congressional oversight is that many Members of Congress are deeply reliant on staff to dig into intelligence reports, analyze what they are reading, and come away with critical insights into the surveillance activities of U.S. federal intelligence and law enforcement agencies. In the House, most Members do not even have staffers with high levels of security clearance to perform this function. Thus, free of strong Congressional oversight, federal agencies “spy first, ask for forgiveness later,” says Jake Laperruque of the Center for Democracy and Technology. As a result, Laperruque says, “violations are epic in scale.” When federal agencies are caught stretching or breaking the laws they respond with a charade of addressing rule-breaking with tighter rules. Thus, Laperruque adds, agencies follow a tried-and-true formula of “violate, tweak rules, repeat.” These are just some of the nuggets from an hour-long conversation between Goodlatte, Laperruque, Liza Goitein of the Brennan Center for Justice, in a discussion moderated by Cato Institute senior fellow, Patrick Eddington. Watch and you will learn about the origins of foreign surveillance authorities used by agencies to spy on Americans, as well as why Bob Goodlatte believes that simply allowing one of them, Section 702, to expire would be a mistake. (Go to 36:00 mark). John Greenwald at The Black Vault reports a curious change in the responsiveness of the National Security Agency to Freedom of Information Act (FOIA) requests regarding Intellipedia, a shared source within the intelligence community.
This online system gives the intelligence community a collaborative way to share information, insights, and theories across agencies, breaking down many of the barriers that restricted sharing of intel pre-9/11. Intellipedia consists of wikis that contain “Top Secret Sensitive Compartmented Information,” “Secret Information,” and “Sensitive But Unclassified Information.” Think of it as Wikipedia for spies. For years, NSA had routinely released articles and category pages that reside in this digital resource. The Black Vault filed FOIA requests with NSA – which handles such requests for Intellipedia – to obtain glimpses into the unclassified collaborative thinking of the intelligence community. Greenwald writes that in 2017, a successful FOIA appeal revealed that Intellipedia had more than 50,000 content pages in the unclassified section; more than 114,000 content pages in the “Secret” section; and more than 124,000 pages in the “Top Secret” section. It also included, he writes, “millions of additional pages within those three systems that includes other wiki pages, talk pages, and redirects, and finally, the three systems hold more than 600,000 uploaded files for download.” He postulates that these numbers are likely much larger five years later, a reasonable guess considering the swelling numbers of classified documents across government. The NSA, despite having released unclassified articles and pages for over a decade, is now issuing the all-too common Glomar response – neither confirming nor denying the existence of requested documents – and turning to statutory exemptions that it failed to invoke for over that ten years. What changed? “This sets a concerning precedent,” Greenwald writes, “as it suggests that government agencies might have the ability to bypass the established FOIA exemptions and deny information requests based on internal policy decisions made on a whim.” In our experience, the evolution of the Glomar response into an all-purpose stonewall is the rule. Intellipedia was a refreshing exception, perhaps a reflection of the creative impulse of the people behind it. Now it’s just like everything else in the government – even with unclassified information, it’s strictly need to know, old chum, and you don’t need to know. George Kennan, an American diplomat living in Moscow in 1946, penned the “long telegram” that defined the Cold War in 8,000 words. Elizabeth Goitein, Senior Director of the Brennan Center for Justice’s Liberty and National Security Program, has written – at about one-half the length of Kennan’s telegram – an article in Foreign Affairs that is another landmark piece that in lucid prose describes the essentials of living in an “era of unprecedented government surveillance.”
Goitein’s piece centers around Section 702 of the Foreign Intelligence Surveillance Act, designed by Congress to allow targeting foreigners on foreign soil for intelligence purposes. Congress foresaw the need to include measures to protect Americans whose communications are incidentally caught up in this web of surveillance. The law stipulates that the government must “minimize” the collection, sharing, and retention of Americans’ information. And the government must certify that it is not engaging in “reverse targeting,” using the surveillance to work backwards to obtain the communications of particular Americans. Elizabeth Goitein then contrasts the intentions of Congress and the reality of Section 702 in practice: “Fifteen years into the program, it is clear that these protections are not working. The government, with the FISA Court’s backing, has adopted a remarkably maximal interpretation of minimization. After collecting the data, the NSA routinely shares portions of it—including Americans’ communications—with the CIA, the FBI, and the National Counterterrorism Center. All agencies retain the data for at least five years, and in some cases, such as when the data is encrypted, much longer. “The most controversial aspect of the program, however, is the use of ‘backdoor searches’ (or, as the government refers to them, ‘U.S. person queries’): the practice of electronically searching the Section 702–acquired data to find and retrieve Americans’ phone calls, text messages, and emails. In other words, having obtained the data without a warrant by certifying that it is not seeking access to the communications of particular, known Americans, the government then intentionally searches that very data for the communications of particular, known Americans.” You know you’re in the hands of a skillful writer when she steps back and just lets the facts convey the irony. Goitein goes on to detail reforms to Section 702 that should be a prerequisite for its reauthorization before this authority sunsets at the end of this year. But she makes it clear that this is just one tool the government uses to spy on Americans. Another is the purchasing of our most sensitive personal information by government agents from data brokers. Yet another is bulk collection of data under 12333 – authorized not by a statute, but by an Executive Order. “In short, the United States is long overdue for a rightsizing of government surveillance,” Goitein writes. “The reauthorization of Section 702 provides the best opportunity Congress has had since 9/11, and perhaps will have for a long time, for that undertaking … But unless Congress is willing to attack the other heads of the Hydra, it will have done little to rein in warrantless surveillance of Americans.” In a recent response to a Freedom of Information Act request PPSA submitted in 2020, the National Security Agency released a record showing an exponential – no, make that mind-blowing – increase in the number of “derivative classification” decisions.
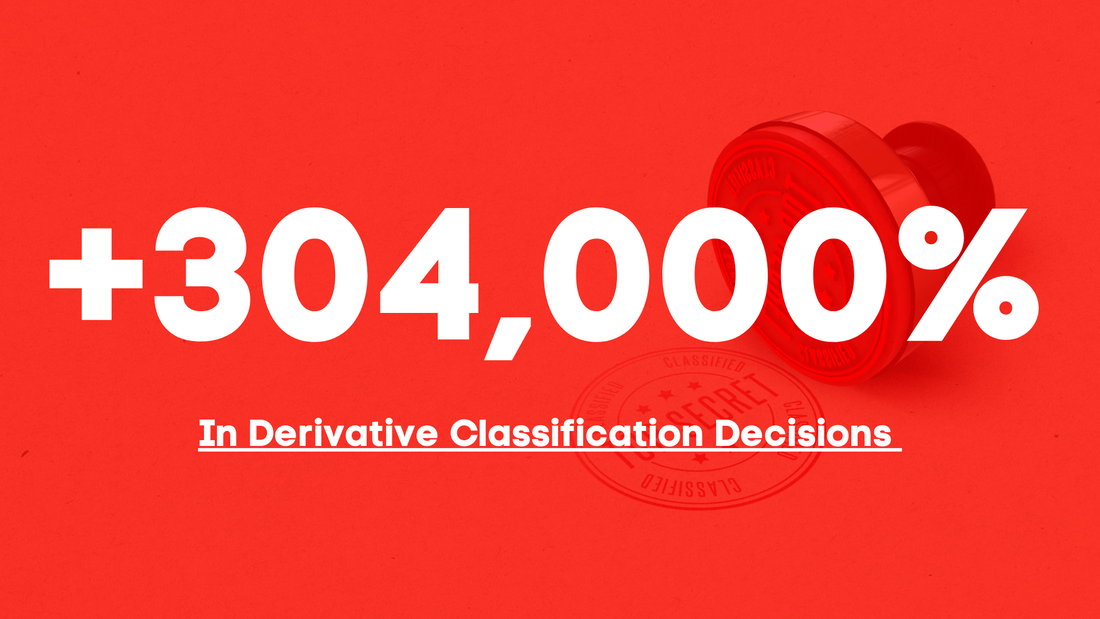
In plain English, “derivative classification” describes the decision to classify a document because it incorporates, paraphrases, restates, or generates in new form information that is already classified. Makes sense, right? Now explain this. NSA released forms showing that the number of derivative classification decisions in just that agency increased from approximately 11,500 in 2007-2008, to over 20 million in 2008-2009, and to more than 35 million in 2010. That’s an increase of more than 304,000 percent! And, while recent years have seen a decrease – 23 million in 2013 and 7 million in 2017, these are still eye-popping increases over the 2008 level of 11,544. What might explain this explosive reliance on derivative classification? Perhaps it is a response to President Obama’s Executive Order 13526, which was meant to stem the tide of classified documents and to prevent agencies from classifying documents “for self-serving reasons or simply to avoid embarrassment.” Does the explosive increase in derivative documents decisions represent the bureaucracy’s work-around President Obama’s order? Overtly classified documents grew from 55 million when President Obama issued his order to 77.5 million five years later. Are these newly released numbers evidence the government is using the derivative classification mechanism to enlarge the classified state even more? Yet another good question for Congress to ask. In the meantime, PPSA has recently filed a Freedom of Information Act request asking NSA, as well as the FBI and Office of the Director of Intelligence, to produce documents that would explain wild fluctuations in derivative classification and increases in hiring and software purchases to handle such volumes. We will report any details PPSA receives that might explain this explosive growth of derivative classification. Much of the congressional debate about the reauthorization of Section 702 of the Foreign Intelligence Surveillance Act concerns the paradox that an authority designed by Congress to spy on foreigners on foreign soil has been used by U.S. government agencies to spy on Americans – 278,000 warrantless searches of Americans in a recent one-year period.
The U.S. debate understandably revolves around Americans’ concern about our government spying on us. But it shouldn’t come as a surprise that Europeans – who enjoy no Fourth Amendment protections under U.S. law – are also not thrilled by the idea that the U.S. government freely accesses their private information and communications. European frustration with the U.S. government’s appetite for surveillance is becoming a source of major trade friction with the United States. In 2020, the European Court of Justice struck down a U.S.-EU data flow agreement known as the Privacy Shield precisely because of concerns about the aggressive use of surveillance by U.S. intelligence services. The EU and U.S. appear to be finalizing a new data flow deal this summer. But this deal could be upended by continuing rows between the two economic zones over surveillance. The Irish Data Protection Commission in late May found Meta – owner of Facebook – in violation of Europe’s General Data Protection Regulation when it transferred the personal data of Facebook users to the United States without sufficiently protecting them from U.S. government surveillance. The EU followed up by enforcing Ireland’s finding with a fine of €1.2 billion. Meta will appeal. Even for Meta, this is an eye-popper of a fine. But it is perhaps small potatoes compared to the potential cost to the more than 5,000 U.S. companies that do business in Europe if a data sharing agreement cannot be reached. To be fair, there is a bit of disingenuousness here. There is sometimes a whiff of protectionism in Europe’s high-minded critiques of companies that, surprise, always turn out to be American. And EU countries are hardly innocent when it comes to spying. They have massive surveillance operations targeting Americans, as well as their own citizens, with no Fourth Amendment protections offered under their law. But the issue remains that Europe is demanding that its private citizens who are not likely to communicate information about foreign threats not be targets of routine U.S. surveillance. Congress will, of course, maintain foreign intelligence. But if it places reasonable limits on surveillance generally, and especially bulk surveillance, and if it removes barriers to judicial review of surveillance, those steps alone might be enough to rebuild trust with Europe. Reforming FISA would help as well. Simply applying a warrant standard for U.S. persons would go a long way in demonstrating to Europe that the United States is turning the page on unrestrained surveillance. |
Categories
All
|




















 RSS Feed
RSS Feed