|
PPSA recently reported that the Bureau of Alcohol, Tobacco, Firearms and Explosives (ATF), in a response to our Freedom of Information Act (FOIA) request, downplayed its use of stingrays, as cell-site simulators are commonly called. Yet one agency document revealed that stingrays are “used on almost a daily basis in the field.” This was a critical insight into real-world practice. These cell-site simulators impersonate cell towers to track mobile device users. Stingray technology allows government agencies to collect huge volumes of personal information from many cellphones within a geofenced area. We now have more to report with newly-released documents that, as before, include material for internal training of ATF agents. One of the most interesting findings is not what we can see, but what we can’t see – the parts of documents ATF takes pains to hide. The black ink covers a slide about the parts of the U.S. radio spectrum. Since this is a response to a FOIA request about stingrays, it is likely that the spectrum discussed concerns the frequencies telecom providers use for their cell towers. What appears to be a quotidian training course for agents on electronic communications has the title of the course redacted. If that is so, was there something revealing about the course title that we are not allowed to see? Could it be “Stingrays for Dummies?” The redactions also completely cover eleven pages about pre-mission planning. Do these pages reveal how ATF manages its legal obligations before using stingrays? This course presentation ends somewhat tastelessly, a slide with a picture of a compromised cell-tower disguised as a palm tree. In the release of another tranche of ATF documents, forty-five pages are blacked out. It appears from the preceding email chain that these pages included subpoenas for a warrant executed with the New York Police Department. The document assigns any one of a pool of agents to “swear out” a premade affidavit to support the subpoena. The ATF reveals it uses stingrays on aircraft, which requires a high level of administrative approval. It seems, however, from an ATF PowerPoint presentation that this is a policy change, which suggests that prior approvals were lax. Was this a reaction to the 2015 Department of Justice’s policy on cell-site simulators? If aerial surveillance now requires a search warrant, what was previously required – and how was such surveillance used? Was it used against whole groups of protestors? Finally, the documents reveal that the ATF has had cell-site simulators in use in field divisions in major cities, including Chicago, Denver, Detroit, Houston, Kansas City, Los Angeles, Phoenix, and Tampa, as well as other cities. PPSA will report more on ATF’s ongoing document dumps as they come in. By The Way... Here's How ATF Glosses Over Its Location TrackingThe training manual of the Bureau of Alcohol, Tobacco, Firearms and Explosives states that cell-site simulators “do not function as a GPS locator, as they do not obtain or download any location information from the device or its applications.” This claim is disingenuous. It is true that exact latitude and longitude data are not taken. But by tricking a target’s phone into connecting and sending strength of signal data to a cell tower, the cell-site simulator allows the ATF to locate the cellphone user to within a very small area. If a target uses multiple cell-site simulators, agents can deduce his or her movements throughout the day.
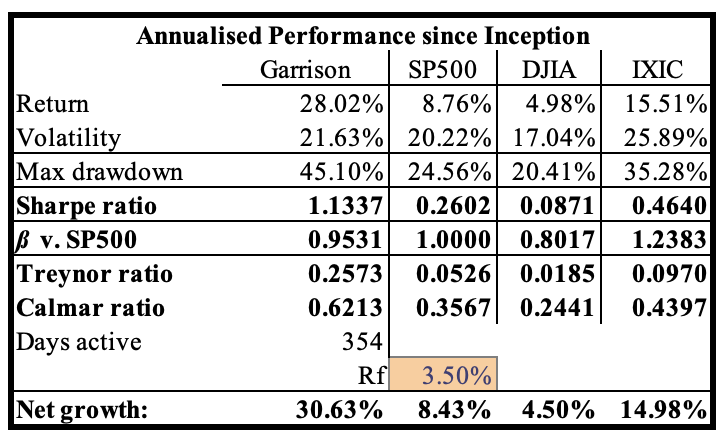
Below is an example from a Drug Enforcement Agency document that shows how this technology can be used to locate a target (seen within the black cone) in a small area. Comments are closed.
|
Categories
All
|


 RSS Feed
RSS Feed