|
Charles C.W. Cooke in National Review recently penned a provocative essay that says what some conservative Republicans and progressive Democrats are thinking – dismantle the FBI!
Cooke makes a case that ever since J. Edgar Hoover took over the Bureau of Investigation, the FBI has been “a violent, expansionist, self-aggrandizing, and careless outfit that sits awkwardly within the American constitutional order.” Cooke presents the FBI’s parade of horribles: J. Edgar Hoover presented President Truman with a plan to suspend habeas corpus and put 12,000 Americans into military facilities and prisons at the outbreak of the Korean War. The FBI under Hoover’s leadership tried to convince Dr. Martin Luther King Jr. to commit suicide. It helped presidents destroy their enemies and used blackmail to intimidate the FBI’s critics (paranoia fueled from the likely fact that Hoover himself was eminently blackmailable). It doubled down on a macho confrontation with David Koresh, clearly a psychopath, leading to the deaths of 75 people, 17 of them children. We would add to that list a bureau headquarters that actively blocked investigations from the field that could have stopped 9/11. Many have more recent reasons to suspect the FBI is rigging its investigations. In recent years, an FBI lawyer was caught and convicted of presenting altered evidence and lying to the Foreign Intelligence Surveillance Court in an effort to hide Carter Page’s service to the CIA. The FBI today has excellent justification to pursue those who invaded and trashed the U.S. Capitol on Jan. 6, and perhaps reason to pursue an investigation of former President Donald Trump’s handling of classified material – but these investigations will always be suspect to millions of Americans because of the FBI’s involvement in partisan forgery and in peddling the Steele Report, which the FBI knew at the time was unreliable. On the other side of the ideological fence, the FBI has employed invasive surveillance techniques to spy on Americans who exercised their First Amendment rights by protesting police misconduct. So Cooke’s cry to dismantle the FBI, once a fringe opinion, is sure to have resonance with many on the right and left. As outrageous as the FBI has been at times, however, we counsel critics remember its value in keeping us safe from terrorists, human traffickers, cyber-criminals and foreign intelligence agents from Russia and China. And make no mistake, Russian and Chinese agents and their subordinated or blackmailed helpers are in America in force and doing great harm to our country. Fighting these threats are some of the most capable and patriotic men and women we’ve ever met. So what to do? Cooke offers a list of potential reforms he had toyed with before deciding to argue for the wholesale dismantlement of the FBI. Cooke’s list is well thought-out and worthy of a second look and of being quoted at length:
We endorse Cooke’s strong list of reforms, to which we propose two of our own.
In looking at the history of the FBI, strong leadership has often come from its field offices. But leadership in the top tiers of the J. Edgar Hoover Building has shown itself to be entrenched with Washington power-seeking and socially enmeshed with media and political circles. If one wants to bring about change, perhaps a good place to start would be to divert resources taken up by HQ and spread them out of Washington and into the field offices. Andrew McCarthy, in a reply to Cooke in National Review, promotes the idea of separating the intelligence function of the FBI from its law enforcement function. This would return the FBI to being an agency dedicated solely to law enforcement. It would create an American version of the UK’s MI-5 for the purpose of counterintelligence. Like MI-5, the new agency would have no police powers (though the creation of a 19th intelligence agency in the U.S. government would undoubtedly bring fresh concerns about surveillance and privacy). Another needed change would be to instill into the culture of headquarters something similar to that of the senior ranks of the U.S. military, which eschews any sign of partisanship. Many generals and admirals will not discuss their political views. Some make it a point of pride not to vote. This may be asking too much of civilian officials, but if an agent is assigned to a team that deals with political crimes, with First Amendment implications that resonate nationally, being an outspoken partisan should be reason enough for an immediate transfer to some other important line of duty. Eight years ago, the U.S. Supreme Court held in Riley v. California that because cellphones hold “the privacies of life” – in the form of texts, images, emails, calls and more – that police (barring extreme circumstances) need a warrant to search it.
The application of a new legal standard, however, is never so simply adopted. Ever since, federal and state courts have applied Riley in contradictory ways. To cite just one example, the Montana Supreme Court recently came down hard on the side of digital privacy. As we reported in February, parolee Bradley Mefford was challenged for leaving his apartment by parole officer Jake Miller. Mefford told his parole officer that he merely went into the parking lot to get reception to engage a Facebook Messenger conversation with his daughter. He gave the officer permission to read his Messenger thread to prove he was communicating with his daughter. The officer took the phone and surveilled all its contents, including images. Beyond Messenger, Miller found evidence of a serious crime. The ACLU vigorously defended Mefford’s cellphone privacy rights. Montana’s high court agreed, vacating the charges stemming from that officer’s sweeping, generalized surveillance. The court found: “It was no more reasonable for Miller to believe he had permission to search Mefford’s photos to corroborate the identify of his daughter than it would have been for him to search through a photo album in Mefford’s bedroom or a rolodex on Mefford’s office desk for information regarding Mefford’s daughter.” Other courts have come down on opposing sides. EFF’s Jennifer Lynch and Allie Schiele offer a sweeping look at recent rulings. They write that “some courts have constrained police searches to certain types of data on the phone, specific time periods, or limited the use of data, other courts have authorized warrants that allow the police to search the entire phone.” In United States v. Morton, the Fifth Circuit sitting en banc overturned a panel opinion that had overturned a broadly executed warrant. The court upheld a “good faith exception” that “evidence should not be suppressed when law enforcement obtained it in good-faith reliance on a warrant.” Dissenting judges wrote: “Searching a cellphone is much more invasive than a self-contained search of a pocket compartment or a bag.” The dissenters also complained that the affidavit was supported by “sweeping generalizations,” a precedent that allows officers to hide behind the good-faith exception – which is “unjust, unfair, and unconstitutional.” In Richardson v. State, the Maryland Court of Appeals found that “the privacy concerns implicated by cellphone storage capacity and the pervasiveness of cellphones in daily life do not fade away when police obtain warrants to search cellphones.” Maryland’s highest court held that there is no “one size fits all” solution for cellphone searches. Some might search within a specific timeframe or confine the search to an app or set of apps, or other restricted search protocols. Ultimately, the Maryland high court found, “a search warrant for a cellphone must be specific enough so that officers will only search for the items that are related to the probable cause that justifies the search in the first place.” EFF’s Lynch and Schiele conclude that Maryland sets the right precedent, writing that courts should “require cellphone warrants that are narrowly tailored to the crime under investigation.” PPSA agrees. We also acknowledge, however, that such restrictions sometimes impose a cost at the expense of justice. In the Mefford case the underlying charges vacated by the Montana court arose from child pornography discovered on the parolee’s phone. In the Maryland case, a search of multiple phones of a high school student who had carried a gun to school showed evidence that he was planning a robbery (though in that case, the court did not vacate the evidence). Painful tradeoffs arise when weighing privacy against policing, sometimes hard to stomach. We must remember, however, that such limits on cellphone searches are needed to prevent the United States from becoming a surveillance state. Judge Rudolph Contreras, of the U.S. District Court for the District of Columbia, gave PPSA a victory in our quest to compel the FBI to search and possibly produce correspondence between Members of Congress and agencies about their “unmasking.”
More than one year ago, PPSA filed suit to follow up on a Freedom of Information Act (FOIA) request asking the FBI to produce documents about the potential unmasking or identification of individual members of Congress whose messages are caught up in intercepts of foreign communications. We specifically asked for correspondence between House Members and Senators with federal agencies regarding unmasking. We also asserted that since the Gates Procedures – the method by which congressional identities are handled and can be deanonymized – are in the public domain, the FBI cannot issue a Glomar response, which neither confirms nor denies the existence of such records. Judge Contreras denied this broader motion, saying it wasn’t relevant to the core request about acquiring correspondence. But he found merit with the other request about correspondence. The judge wrote: “But there exists a separate category of documents: communications between the FBI and Congress that are a degree removed from FISA-derived documents and which discuss congressional unmasking as a matter of legislative interest, policy, or oversight … The FBI must conduct a search for any ‘policy documents’ in its possession.” FBI attorneys had argued that the core of our request was for “operational documents” concerning congressional unmasking. Judge Contreras rejected that contention, noting there are not necessarily any law enforcement procedures, techniques, or guidelines “that would risk circumvention of the law … because acknowledging the existence of congressional inquiries would not necessarily reveal anything about the FBI’s operations.” Such policy documents are “well within the four corners of the FOIA request.” If the FBI follows it traditional path and issues a Glomar response anyway, PPSA will be there to press further litigation. And we will report any findings with alacrity. Samantha Murphy Kelly of CNN Business news has a snappy take on Amazon’s recent product press event. The company, she wrote, “knows when you’re in and out of the room. A gadget that monitors your breathing pattern while you sleep. An enhanced voice assistant that highlights just how much it knows about your everyday life.”
She notes another event where Amazon introduced drones and Astro, a dog-like robot that can patrol the home when you’re gone. Will consumers be deterred by the creep factor of giving so much of our personal information taken from the intimacy of our homes? Kelly quotes a consumer analyst who said that “negative consumer attitudes” about data collection is lessened by the service, price, and convenience of these products. It is easy to see why consumers are sanguine about sharing data with a company that sells products and services they like. All Amazon wants to do is to sell us even more products. Dangers emerge, however, when consumer data migrates beyond the company you’re doing business with. Amazon, for its part, says that “information about our customers is an important part of our business, and we are not in the business of selling our customers’ personal information to others.” The company does share information with third parties, such as vendors whose goods are sold through Amazon. A recent FTC filing against the data broker Kochava shows that Amazon Web Services Marketplace allows companies to buy consumers’ IP addresses and precise geolocation histories. Amazon also encourages its Ring customers to share their data with police agencies across the country – creating a national surveillance network stitched together from more than three million cameras. Whatever the limits of Amazon’s privacy policies, most of the other major social media platforms freely sell consumer data to brokers. Among the major customers of this data, as PPSA has endlessly reported, are the intelligence and law enforcement agencies of the U.S. government – reason why PPSA has joined with almost fifty other civil liberties organizations to call for the passage of the Fourth Amendment Is Not for Sale Act. Your dog may follow you around the house, but she will never judge you. Not so with the many devices that are infiltrating into our lives. The first responsive information from the Office of the Director of National Intelligence to a Freedom of Information Act (FOIA) lawsuit for records concerning U.S. intelligence purchases of the private data of American citizens is trickling in. As often happens, cursory information allows us to catch a glimpse of secret practices, if only through a glass darkly.
The ears of civil libertarians perked up when Director of National Intelligence Avril Haines (1:17:05 mark) in her Senate confirmation hearings in early 2021 was asked about purchases of Americans’ data by Sen. Ron Wyden, (D-OR). She responded: “I would seek to try to publicize, essentially, a framework that helps people understand the circumstances under which we do that and the legal basis that we do that under.” Haines further promised to provide transparency “so people have an understanding of the guidelines under which the intelligence community operates.” On May 17, 2021, PPSA requested records related to statements by Director Haines concerning the promise to publicize the circumstances under which the U.S. intelligence community purchases Americans’ private data, and its legal basis for doing so. After one year of awaiting a response – long past the statutory deadline – PPSA filed a lawsuit in July 2022 to press ODNI to respond to the request. PPSA announces today that it received a reply that ODNI conducted a search and found approximately 1,000 emails potentially responsive to our request. ODNI, however, explains that it does not have “de-duplication” software that would winnow the body of records to single copies. This is remarkable, since almost every other executive agency has such software, including many under ODNI’s purview. Searches of the documents will have to be done by hand and eye. With personnel changes, ODNI explains, it can only begin releasing records in late November – eighteen months after the submission of the FOIA request and in the middle of the holiday and travel season. PPSA filed a motion asking a federal court to require ODNI to process at least 500 pages of records a month. “What is most interesting about ODNI’s response,” said Gene Schaerr, general counsel of PPSA, “is that it has perhaps a thousand emails about living up to Director Haines’ promise of a degree of transparency without referring to a single document that would actually indicate that the office is transparent.” PPSA will release more information from this legal action as ODNI produces results. A new report by the United Nations Human Rights Council highlights how much of a global issue spyware has become. The Office of the High Commissioner for Human Rights calls for greater attention to threats to data privacy, to the development of state-sponsored spyware capabilities, and especially to the dangerous software Pegasus, which can remotely infiltrate smartphones and turn them into spying devices. PPSA has reported in the past on the emerging threat Pegasus poses to nations and individuals around the world. It is heartening to see the UN take this data privacy crisis seriously as a human rights issue.
The UN report focuses on three core trends relating to the role of member states in safeguarding and promoting the right to privacy:
The report draws special attention to Pegasus. “The extent of Pegasus spyware operations and the number of victims are staggering… Reporting in 2021 revealed that at least 189 journalists, 85 human rights defenders, over 600 politicians and government officials, including cabinet ministers, and diplomats were affected as targets.” The report notes that at least 65 governments have acquired commercial spyware surveillance tools. NSO Group, the Israeli company that developed Pegasus, reported that 60 government agencies in 45 countries are among its customers. The UN report states: “While purportedly being deployed for combating terrorism and crime, such spyware tools have often been used for illegitimate reasons, including to clamp down on critical or dissenting views and on those who express them, including journalists, opposition political figures and human rights defenders…” The report also condemned efforts by governments to undermine the security and confidentiality of encrypted communications – a key goal not just of repressive regimes, PPSA would add, but of some in the Department of Justice and FBI. Governments continue to take steps to undermine that privacy, either by legislative fiat or by sophisticated hacking techniques. In some countries, encryption providers have been required to ensure that law enforcement or other government agencies have access to all communications upon request, effectively obliterating any privacy that encryption may have provided. This is a brave report. PPSA is pleased to see the UN Human Rights Council recognize privacy as a human right, contrary to the practice of repressive governments, including China and Russia, which have seats on the UN Security Council. Unfortunately, the UN’s warnings on pervasive surveillance also need to be taken seriously by democratic governments, including some in positions of authority in the United States. If you thought being subjected to “random” TSA screenings at airports was dehumanizing, just imagine your most sensitive, personal digital information being secretly reviewed by any one of thousands of government agents operating without a warrant or public oversight.
The Customs and Border Protection Commissioner Christopher Magnus revealed to Sen. Ron Wyden (D-OR) that the agency is scooping data from thousands of seized electronic devices every year. (Hat tip to Drew Harwell of The Washington Post for detailing this abuse of privacy.) That data is then added to a CBP database accessible by more than 2,700 CBP agents. That data – which can include call logs, messages, contact lists, and photos – can be kept for up to 15 years. This story is just the latest development in a long-running series of data privacy breaches by federal law enforcement officials. Sen. Wyden criticized the agency for “allowing indiscriminate rifling through Americans’ private records.” CBP conducted more than 37,000 searches of travelers’ devices in the 12 months ending in October 2021. According to The Washington Post, the default configuration for some data searches has been to download and retain all contact lists, call logs and messages. This means potentially millions of calls, contacts, and text messages from thousands of phones could be compromised. It has long been known that CBP makes generous use of the “border search” exception in Fourth Amendment law. Sen. Wyden’s revelation about the scale and the scope of this loophole reveals an egregious new threat to the security of Americans’ data privacy. Congress must act now to bolster protections for data privacy. It is high time for the Supreme Court to review and modify the judicially created border search exception in light of the massive amounts of information being seized from law-abiding citizens and then stored for long periods of time. If the Court does not protect the Fourth Amendment, then Congress should step up. Last year, Sens. Wyden and Rand Paul (R-KY) introduced legislation that would require border officials to get a warrant before searching a traveler’s device. Congress should also pass the Fourth Amendment Is Not for Sale Act to ensure this database doesn’t fall into the hands of data brokers. Last week, PPSA reported on Fog Reveal, a product from Fog Data Science that sells billions of data points extracted from apps on 250 million mobile devices to local police departments. An unlimited-use, one-year subscription costs a department only $7,500.
For this price, Fog Reveal offers a powerful capability, the ability to track hundreds of millions of Americans in their daily movements. It allows police to locate every device in a given geo-fenced area. It also allows police to trace the location history of a single device (and therefore, its user) over months or years. Fog Data Science claims that it is respectful of privacy because it does not reveal the names or addresses of individual users. But a slide show from Fog Data Science prepared for police highlights how this technology can easily be used to track a suspect to his or her “bed-down” over a 180-day period. (Hat tip to the Electronic Frontier Foundation, which helpfully added yellow highlights to significant passages of Fog documents.) It is more than a stretch then to call this data “anonymized” when it follows people to their homes, as well as to their houses of worship, meetings with friends or lovers, trips to health or mental health clinics, journalists meeting with whistleblowers, or other locales that reveal sensitive and personal information. For those in law enforcement who go through the motions of filing a warrant, Fog Data Science offers a template warrant. Such warrants are misbegotten. They can be employed to follow a number of people in the vicinity of a crime or track everyone who attended a political protest. The Fourth Amendment requires “probable cause” in which a warrant describes “the place to be searched, and the persons or things to be seized.” It makes a mockery of the Constitution’s requirement for particularity when the police have at their fingertips a whole ocean of data involving many people. How can such a requirement be fulfilled when Fog technology allows police to go on a fishing expedition in that ocean, with any American potentially being a catch? It is through technologies such as Fog Reveal that our country, device by device, is moving steadily toward becoming a full-fledged surveillance state. Such details should spur Congress to investigate the uses of this technology. It should also inspire Congress to pass the Fourth Amendment Is Not for Sale Act, which would block the auctioning of our private, personal information to all government agencies. An elegant essay by Adrian Wooldridge in Bloomberg makes a connection between the Chinese surveillance state – “using the awesome power of data harvesting and artificial intelligence to compile more information on its citizens than any society has ever managed before” – and Western “surveillance capitalists” who are making our country a little more like China day by day.
PPSA has long warned that all the elements are falling into place to create an American surveillance state. Here are just a few of the ways in which this is happening: The federal government and local police departments use “stingray” technology to trick Americans’ phones to betray your location and other personal information. Authorities can purchase your location history with Fog Reveal technology and capture all your comings and goings. Or they can just buy your personal information from a private data broker, as many federal agencies do. The growing web of the “internet of things” will only produce more reportable data about you, from the cars we drive, to our refrigerators and other appliances in our home. A surveillance loophole was even recently found in a Chinese-made coffee maker. Wooldridge reports that the Chinese Communist Party is at the cutting edge, “developing a new sort of ‘digital phrenology’ by monitoring people’s facial expression for signs of anger and new forms of racial profiling by creating a world-leading DNA database.” Governments, including our own, exert “relentless pressure for the misuse of information even as the quality and quantity of available information grows exponentially.” The techno-optimists of the 1990s waxed rhapsodic about how the internet was going to liberate the human mind. Wooldridge comes to an opposite conclusion with these chilling words: “The arc of the digital revolution bends toward tyranny.” Agencies Avoid Answering Questions About the Purchase of Private Information of Members of CongressSince the mid-1960s, the Freedom of Information Act (FOIA) has allowed American citizens and civil liberties organizations to obtain unclassified documents from federal agencies, shedding light on official actions and policies. In recent years, however, the government has devised many creative ways to stall, obfuscate, and outright withhold answers to FOIA requests, while seeming to be as responsive as possible. Cato Institute scholar Patrick Eddington calls these tactics “constructive denial.”
For over two years, Cato filed FOIA requests to obtain FBI records on militia groups of the left and the right, including the white supremacist Patriot Front. “Groups like the Patriot Front,” Eddington writes in The Hill, “are, in the view of most Americans, a moral and political blight that the country would be far better off without. At the same time, the protection of offensive ideas and speech are at the heart of the purpose of the First Amendment.” Thus, Cato sought records to better understand the threat posed by these groups and the nature of the government’s response. In defiance of FOIA’s requirement that the FBI send the requested documents to the requester himself, the FBI replied to Cato that it would eventually file the documents on an FBI website. “You will be notified when releases are available.” In other words, buzz off. Constructive denial can be seen in another form after PPSA filed suit against the National Security Agency, the CIA, the Department of Justice and FBI, and the Office of the Director of National Intelligence in June to compel the release of records pertaining to the possible purchase of the personal information of more than 100 current and former Members of the House and Senate Judiciary Committees from private data brokers. This is understandably a sensitive question, given that current and former judiciary committee lawmakers include Chairman Jerrold Nadler, Ranking Member Jim Jordan, Chairman Dick Durbin, Ranking Member Chuck Grassley, as well as Vice President Kamala Harris and Florida Gov. Ron DeSantis. Still, it would be a matter of public interest – not to mention to these legislators themselves – if the government were buying up their personal information. Such an act could yield leverage for executive branch agencies to bully leading Members of Congress, subtly undermining democracy. The agencies’ response to PPSA’s FOIA request over summer 2021 was to issue Glomar responses, a judicially invented doctrine that neither confirms nor denies that such records exist. Now that PPSA has sued to enforce its request, these agencies have come back with an answer that doubles down on a government theory that it would be too dangerous to national security for these agencies to even search for such documents. At the same time, government responses strike a tone of wanting to be as cooperative as possible. One choice example: PPSA asserted a “right of prompt access to requested records under the law.” The National Security Agency responded: “To the extent that a response is required, Defendant NSA denies the allegation, including the fact that NSA has wrongfully withheld records.” This is a construction worthy of Joseph Heller’s Catch-22. Gene Schaerr, PPSA general counsel, responds: “The government’s answers disingenuously conflate an internal search for documents with an external response to a question. The government feels free to treat FOIA as polite supplication instead of a law that must be obeyed. PPSA will continue to press on for a serious answer in federal court.” In the meantime, expect the government to come up with many new forms of constructive denial. PPSA recently reported that prosecutors charged two Twitter employees with being spies for Saudi Arabia. One of the men fled the country. The other was convicted.
Now, more bad news for Americans concerned about privacy. While Twitter’s shareholders were approving the $44 billion sale of their company to Elon Musk on Tuesday, Peiter Zatko, Twitter’s former head of security, testified before the Senate Judiciary Committee about the state of security inside the social media platform. Zatko said that the FBI had informed him that at least one agent of China’s Ministry of State Security was “on the payroll inside Twitter.” Zatko told the senators: “I discovered that the company had ten years of overdue critical security issues, and it was not making meaningful progress on them. This was a ticking time bomb of security vulnerabilities.” He added that he made the decision to inform the FBI, which led to his dismissal. “In those disclosures, I detail how the company leadership misled its Board of Directors, regulators, and the public. Twitter’s security failures threaten national security, compromise the privacy and security of users, and at times threaten the very continued existence of the company.” In his more than two hours of testimony, Zatko described Twitter’s senior management as deliberately ignoring security issues to protect the bottom line. “It doesn’t matter who has keys if you don’t have any locks on the doors,” he said. “It’s not far-fetched to say an employee inside the company could take over the accounts of all the senators in this room.” At least two agents for the Indian government were on the company payroll, Zatko said, as well as the one from China. Some ads sponsored by the Chinese government appeared to have been designed to specifically capture user information. “Twitter is acting dangerously and negligently to turn its back on user safety,” Nora Benavidez, Free Press senior counsel, told The New York Times. These alleged Twitter breaches, as bad as they are, come on top of a host of similarly disturbing stories about privacy. From foreign infiltration of Twitter, to potential exposure of the data of American TikTok users to Chinese intelligence, to the practice of private data brokers selling Americans’ personal information scrapped from apps to U.S. law enforcement and intelligence agencies – it is clear that we are in a privacy crisis with implications for Americans’ well-being and national security. One way that Congress can respond to that crisis is by passing the Fourth Amendment is Not for Sale Act, which would ban the sale of private data to the government. Once that bill passes, it will be a helpful achievement in creating momentum to deal with all the remaining privacy issues. To quote a line from a great play, “attention must be paid.” A growing number of House and Senate members are supporting the Fourth Amendment Is Not for Sale Act, which would require law enforcement and intelligence agencies to obtain a probable cause warrant before accessing Americans’ personal information purchased from a private-sector data broker.
But what about non-state actors buying our information? A recent lawsuit brought against private-data broker Kochava by the Federal Trade Commission reveals the horrific exposure of Americans’ most personal data to unseen – and possibly unknown – private actors. Kochava claims to have “rich geo data spanning billions of devices globally,” with location data feed that “delivers raw latitude/longitude data with volumes around 94B-plus billion geo transactions per month, 125 million monthly active users, and 35 million daily active users, on average observing more than 90 daily transactions per device.” In its filing on Aug. 29, the FTC writes that a purchaser would only need to provide Kochava a personal email address and describe the intended use as “business” to gain access to your data from Kochava. “The location data provided by Kochava is not anonymized,” the FTC filing asserts. “It is possible to use the geolocation data, combined with the mobile devices MAID (Mobile Advertising ID), to identify the mobile device’s user or owner.” The FTC claims: “Precise geolocation data associated with MAIDs, such as the data sold by Kochava, may be used to track consumers to sensitive locations, including places of religious worship, places that may be used to infer an LGBTQ+ identification, domestic abuse shelters, medical facilities, and welfare and homeless shelters.” It can identify women who visit reproductive clinics and people who attend services at Jewish, Christian, Islamic and other religious denominations’ places of worship. Kochava, the FTC claims, does not employ a blacklist that removes or obfuscates data-set location signals from these sensitive locations. The facts presented by the FTC, as alarming as they are, should not get mixed up in the separate debate on the Hill over restricting the government’s ability to purchase our private data. The many federal agencies that buy our data are not just violating our privacy. They are eviscerating the plain meaning of the Constitution’s Fourth Amendment, which requires government to get a warrant from a court to access our personal information. The solution to private-sector access to personal information is a deep and complex debate taking place within multiple Congressional committees and stakeholders from business and consumer groups. Passing the Fourth Amendment Is Not for Sale Act in this Congress, which would close off the government’s warrantless access to Americans’ personal information, would be a strong predicate for that next step in the privacy debate. In a hearing over the summer, the House Judiciary Committee took a hard look at the way in which private data brokers freely sell Americans most personal information to a host of government law enforcement and intelligence agencies.
Chairman Jerry Nadler said that digital tracking is “so precise that officers can track individuals within specific homes and businesses … tracking your location over time, within inches, without any due process whatsoever. “The end result is that, just by going about your daily life, your data may be swept up in and make you the subject of a criminal investigation … If law enforcement and intelligence agencies remain unrestrained in their ability to purchase this data, our right to privacy will be at best illusory.” Ranking Member Jim Jordan said that the government continues to transform guardrails meant to protect privacy into loopholes to allow the government to do whatever it wants. Jordan said, “this is wrong and it’s un-American.” Representatives of both parties expressed dismay about how freely federal agencies utilize and abuse surveillance powers in defiance of the Fourth Amendment. Rep. Zoe Lofgren detailed the many ways the U.S. Immigration and Customs Enforcement agency tracks Americans’ daily movements and extracts personal information from utility records. Rep. Andy Biggs spoke of the uses to which the government can employ geolocation tracking against Americans. In short, the House Judiciary Committee did an excellent job of teeing up the issue. Now it is time to swing the club for a legislative solution. On Wednesday, PPSA joined with Americans for Prosperity, Demand Progress, the Due Process Institute and Free Press Action to call on the committee to take bipartisan action and mark up the Fourth Amendment Is Not for Sale Act. Local law enforcement agencies have been caught using a cheap new cell phone tracking tool called Fog Reveal. (A hat tip to The Associated Press for compiling this story). The tool gives police agencies “the power to follow people’s movements months back in time,” according to The Associated Press.
Fog Reveal has been used since at least 2018 in criminal investigations, can search billions of records from 250 million mobile devices, and is possibly a potent workaround of the 4th Amendment. It is no wonder why police rarely mention Fog Reveal “in court records, something that defense attorneys say makes it harder for them to properly defend their clients in cases in which the technology was used.” Fog Reveal “relies on advertising identification numbers, which Fog officials say are culled from popular cell phone apps such as Waze, Starbucks, and hundreds of others” according to police emails obtained by The Associated Press. That information is then sold to companies including Fog, further demonstrating the role of data brokers in undermining the digital privacy of Americans. “The capability that it had for bringing up just anybody in an area whether they were in public or at home seemed to me to be a very clear violation of the Fourth Amendment,” said Davin Hall, a former crime data analysis supervisor for the Greensboro, North Carolina, Police Department. Congress must investigate the use of Fog Reveal by law enforcement agencies and bolster legal protections against such 4th Amendment violations. Congress could begin by passing The Fourth Amendment Is Not for Sale Act, which would block data brokers from selling our personal information to law enforcement and intelligence agencies without authorization by a court. Congress must work to ensure the privacy of all Americans is safe and secure. “To exist in 2022 is to be surveilled, tracked, tagged and monitored — most often for profit.” It might sound like an exaggeration, but it’s far from it. When nearly every American is carrying a tracking device, audio and video recorder, and all their personal data in their pocket, nobody is truly private.
The cracks in our digital privacy are getting wider, allowing an almost unfiltered ocean of our most sensitive data to flow into anyone’s hands. As Alex Kingsbury writes in The New York Times: “Consider just last week: Apple released a surprise software update for its iPhones, iPads and Macs meant to remove vulnerabilities the company says may have been exploited by sophisticated hackers. The week before that, a former Google engineer discovered that Meta, the parent company of Facebook and Instagram, was using a piece of code to track users of the Facebook and Instagram apps across the internet without their knowledge. In Greece the prime minister and his government have been consumed by a widening scandal in which they are accused of spying on the smartphones of an opposition leader and a journalist. And this month Amazon announced that it was creating a show called “Ring Nation” — a sort of ‘America’s Funniest Home Videos’ made up of footage recorded by the company’s Ring doorbells.” Just one of these examples should be cause for concern to any American, but the problem is simply too big for individuals to handle. As Kingsbury states, “there are simply too many tech companies, government entities, data brokers, internet service providers and others tracking everything we do.” Congress must take bold action to protect Americans from predatory data collectors and misusers. Legislation like the Fourth Amendment is Not for Sale Act is a step in the right direction. It would prohibit law enforcement and other government agencies from purchasing bulk data from data brokers. In the wake of renewed state battles over the future of abortion rights, the My Body, My Data Act would tighten rules around personal health information. Absent these reforms, “we’re about to find out what happens when that privacy has all but vanished.” PPSA will continue to monitor these issues and fight for privacy in Congress and the courts. Earlier this month, former Vice-President Mike Pence called out criticism of the FBI lodged by members of his own party. In his speech, Pence stated “I … want to remind my fellow Republicans we can hold the attorney general accountable for the decision that he made without attacking the rank-and-file law enforcement personnel at the FBI..” While the intent of Pence’s statement is certainly laudable, it comes at a time when the public is increasingly distrustful of the agency’s activities.
Pence’s comments have been received so poorly because they dismiss the credible concerns emanating from all sectors of the American public. The distrust towards the agency turned into full-blown outrage when the FBI raided former President Trump’s Mar-a-Lago estate earlier this month on August 8th. It has been weeks since the raid, and there has been little official explanation provided. What information we do have has been pieced together from an unsealed warrant and source leaks. From the warrant, the search was related to potential violations of three laws including the Espionage Act. Attorney General Merrick Garland said during remarks on August 11 that he would not explain why he personally signed off on seeking a search warrant. Even though documents were recovered, distrust of the agency has become so severe, that swaths of the American public may choose to believe that the evidence seized was forged and planted. Also worried is Michael Horowitz, Inspector General of the U.S. Department of Justice. Across multiple reports, Horowitz details the abuses, noncompliance, and mishandling that is currently ongoing within the FBI. For a few examples, in September of 2021, the office of the Inspector General released a report stating that there “was widespread non-compliance with the Woods Procedures,” a set of procedures to ensure factual accuracy in FISA applications. In August of 2019, the office of the Inspector General released a report detailing the multiple rules violations by former FBI Director James Comey, indicating a culture of secrecy and noncompliance at the highest level in the chain of command. There are multiple reports detailing commercial sex, accepting illegal gifts from the media, the violation of ethics rules, and a “lack of candor.” When American citizens display “a lack of candor,” they can be fired from their jobs. When senior officials at the FBI do it, prosecution is declined and the offending party is “reassigned to a nonsupervisory role.” In 2019, the Foreign Intelligence Surveillance Court criticized the FBI for misleading it in applications to wiretap former Trump campaign aide, Carter Page. Inspector General Horowitz found that the FBI had omitted facts and provided false statements to the FISA court when the FBI filed for a warrant to conduct surveillance on Page. FISA court presiding Judge Rosemary Collier stated in her opinion that “The FBI’s handling of the Carter Page applications, as portrayed in the OIG report, was antithetical to the heightened duty of candor described above…” So, not only is the public concerned, but so is the office of the Inspector General and the FISA courts, two organizations which either oversee or directly liaise with the FBI. Just this week, the escapades of the FBI were on full display during a trial to convict two men involved in the 2020 plan to kidnap Michigan Governor Gretchen Whitmer. The already high-profile nature of the case was catapulted into the stratosphere when the FBI revealed there were at least five informants or undercover agents embedded among the suspected planners. Defense attorneys have argued there were at least twelve. The involvement of FBI agents and informants was so significant, that a trial for a separate set of suspected planners failed to get a single conviction. One informant became second-in-command of a militia. Another undercover agent offered to provide explosives to the group. It calls into question whether the FBI was engaged in entrapment. FBI agents assigned to the case became subjects of scrutiny themselves. As the New York Times reports, “one F.B.I. agent on the case was fired last year after being charged with domestic violence, and another agent, who supervised a key informant, tried to build a private security consulting firm based in part on some of his work for the F.B.I.…” That FBI agents so close to an ongoing plan to kidnap a governor were themselves so compromised is very chilling. It seems obvious from the last several years that the FBI is in need of both oversight and reform. An agency with significant investigatory and enforcement powers, Congress can and should do more to monitor the activities of the agency. If you think HIPAA medical privacy laws mean your medical data is secure, think again. Digital health companies have been caught funneling sensitive data that patients have shared with them to Facebook/Meta to help target advertisements.
A recent study by the data privacy research group Light Collective surveyed the actions of five health companies and found that third-party ad trackers used by those companies followed patients online and marketed to them based on their activities. Three of the companies went against their own privacy policies in the process, raising concerns about HIPAA violations. Four of the five digital health companies did not respond to requests by Forbes for comment. The authors of the study said that after they disclosed their findings to the five companies, only two responded: Ciitizen and Invitae. Both said they were investigating the matter. Andrea Downing, cofounder of the Light Collective, said that poor health data privacy is “one of the biggest threats to online patient communities.” The study is indicative of larger data-sharing trends across digital health and social media. An investigation published earlier this summer by The Markup showed that hospital websites are currently using data trackers to gather and share sensitive patient information with Facebook for marketing. Facebook’s parent company, Meta, has said that sharing such information is a violation of the company’s rules. This is a concerning development for digital health privacy. Digital health companies are allegedly violating their own privacy rules and possibly the law. It also demonstrates the failure of the government to ensure critical patient health data is safe and secure. A lot has been written about a provision of the upcoming Inflation Reduction Act, which will provide an additional $80 billion in funding to the Internal Revenue Service. Most of this funding will go to bolstering enforcement work, meaning more audits.
While this is bad news for millions of taxpayers, and good news for the makers of Tums Antacid Products for Fast Heartburn Relief, the creation of a new army of auditors is bound to significantly warp the already warped privacy landscape in America. Big numbers for new IRS hires have been estimated. A Treasury Department report from May 2021 estimated that the agency would be able to hire roughly 87,000 employees by 2031 with the additional funding, more than doubling the agency’s staff dedicated to enforcing tax laws. But even media defenses of the plan, which have tried to downplay the number, still estimate anywhere between twenty to thirty thousand new employees. At either number, the IRS expansion will undoubtedly expand the capability of the agency to investigate American citizens. Jonah Goldberg put it best recently when he wrote: “Unlike normal law enforcement, the IRS doesn’t require probable cause to investigate you. It can choose people at random or investigate people based on a theory or a hunch—often sanitized by saying it was the algorithm that made the call. Even if you did nothing wrong, the process itself is punishing and often expensive. One of the bedrocks of our constitutional order, most obviously enshrined in the Fourth Amendment, is the idea that citizens should not be subjected to unreasonable searches without probable cause. Stop and frisk was canceled because it was seen as an outrageous and demeaning affront to civil liberties. I’m conflicted on that. But I certainly get the objections, and I would never say, ‘If you did nothing wrong, you have no reason to complain about being frisked.’ Well, an audit is a forensic frisking of virtually everything you did for a year. What did you spend money on? Where did you spend it? How did you get the money? Show us your receipts. Prove you’re not guilty.” Also concerning are the new methods and technologies the IRS could deploy against the whole country. In February, we reported on the bipartisan resistance to the IRS’s plan to implement facial recognition technology. Under this plan, the IRS would require taxpayers to submit to digital facial recognition scans to obtain tax transcripts and other records. The plan was halted amid significant pushback noting the privacy and technological flaws of facial recognition, but not before 7 million Americans surrendered their biometric data to the IRS and a third-party verification company, ID.me. In May, we reported on the Transparency and Accountability in Service Providers Act, a draft bill circulating that would have deputized millions of “financial gatekeepers” into spying on their clients for the federal government. Virtually the entire financial services industry would be required to report any “suspicious” activity to the government. If the Act were to pass, and the 7.6 million employees of the financial services sector were “deputized,” there would be one informer for every 43 Americans. Where there is a will, there is a way. The IRS is already trying to spy on you. With this new funding, the IRS now has a way. On Tuesday, House Judiciary Committee Chairman Jerrold Nadler and House Homeland Security Committee Chairman Bennie Thompson sent a letter to the heads of key agencies demanding answers to questions about their use of data brokers.
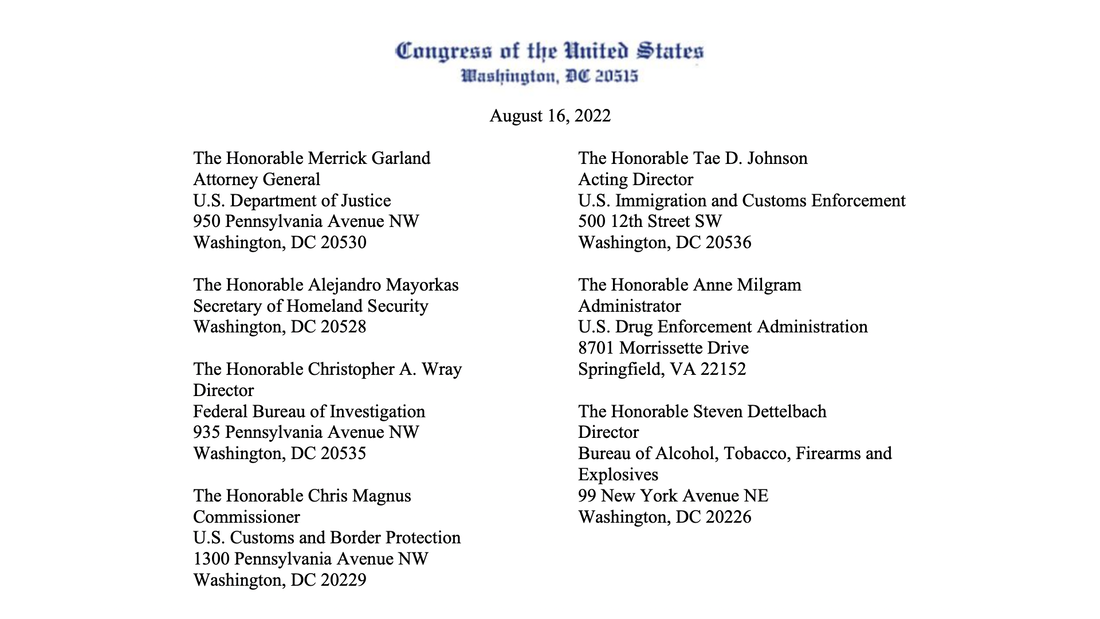
It is no secret that agencies ranging from the FBI to the DEA have been circumventing the Fourth Amendment by purchasing the data of millions of Americans from private data brokers. This letter is the latest sign Congress is waking up to the privacy and surveillance threat posed by data brokers contracting with the federal government. Reps. Nadler and Thompson wrote Attorney General Merrick Garland, FBI Director Christopher Wray, Homeland Security Secretary Alejandro Mayorkas, as well as the heads of Customs and Border Protection, the Bureau of Alcohol, Tobacco, Firearms and Explosives, Immigration and Customs Enforcement and the Drug Enforcement Administration. The two chairmen noted: “In a recent hearing before the House Judiciary Committee, a witness stated that materials provided by data brokers ‘turn policing from a suspect-focused search into a constant, intrusive surveillance system that surveils all of us. Rather than focusing on particular suspects, data policing tools are dragnets, sifting through all of our data.’” The letter demanded each agency provide four sets of documents:
This is a step in the right direction, and PPSA looks forward to further work by Congress on the subject. What we learn from these requests should prompt Congress to pass the Fourth Amendment Is Not For Sale Act. Courts throw out cases in which the government violated the Fourth Amendment to gain evidence obtained illegally. Prosecutors, dreading such a rebuke, have sometimes resorted to “parallel construction” – using illicitly gained knowledge to turn up evidence from a source acceptable in court.
Suppose, for example, that an illegal wiretap by federal investigators reveals that a target will deliver drugs to a certain street corner. They could then alert local police to decide that specific corner is a good place for a spot-check with drug-sniffing dogs. In this way, evidence obtained by illicit surveillance can be laundered. This seems to be especially prone to happen when law enforcement relies on “stingrays” – the common name for cell-site simulators, equipment that mimics a cellphone tower to ping the location of a cellphone. The FBI, in 2014, after providing the Oklahoma City police with stingray technology, sent that department a memo telling the police that the stingray is for “lead purposes” only and “may not be used as primary evidence in any affidavits, hearings or trials.” Instead, the FBI required the police to use “additional and independent investigative means and methods, such as historical cellular analysis, that would be admissible at trial” to corroborate information obtained using the stingray. The Cato Institute’s Adam Bates analyzed such agreements and concluded that “law enforcement uses some surreptitious and, perhaps, constitutionally dubious tactics to generate a piece of evidence. In order to obscure the source of that evidence, police will use the new information as a lead to gather information from which they construct a case that appears to have been cracked using routine police work.” Perhaps because of reporting like Cato’s analysis, formal FBI agreements to sell stingrays to local law enforcement – at least those released to the public – appear to be missing this language. But what about informal agreements? In two responses to PPSA’s Freedom of Information Act requests, the FBI has used similar language in 2015 and 2020 deals to allow police to use stingrays. To be fair, these may be one-off situations. Both cases seem to have been loaner deals, in which stingrays were deployed in “exigent” or emergency circumstances. For example, one 2015 email chain shows that an agency agreed to the FBI’s request that “it is required to use additional and independent investigative means and methods, such as [redacted] that would be admissible at trial to corroborate information concerning the location of the target obtained through the use of this equipment.” Comparing this redacted language to the unredacted provisions imposed on the Oklahoma City police, it appears that the FBI continues to push local law enforcement to hide their stingray use from the courts. On the other hand, this language is missing from other NDA forms PPSA has obtained. Has the FBI abandoned this practice? Or is it continuing “off the books” in some fashion to encourage local law enforcement to launder evidence? Amazon continues its relentless growth as a private data behemoth. On August 5, Amazon announced it will buy iRobot Corp., the maker of the famous Roomba vacuum. While Amazon has an interest in promoting and selling the autonomous vacuum cleaner, it might be far more interested in what the vacuum can collect – and no, it’s not the dirt on your floors.
Great value rests in the Roomba’s ability to map your house, enabled by a technology called Smart Maps. According to iRobot Corp., Smart Maps allow your robot to remember the layout of the inside of your home so you can tailor your house cleaning. Over time as your Roomba develops a detailed map of the layout of your house, the kinds of objects it interacts with can provide critical data about you, your life, and anyone else in your home. For example, Bloomberg reports that “the size of your house,” which Roomba can detect, “is a pretty good proxy for your wealth. A floor covered in toys means you likely have kids. A household without much furniture is a household to which you can try to sell more furniture. This is all useful intel for a company such as Amazon which, you may have noticed, is in the business of selling stuff.” As Amazon continues to develop its smart home line of products, the data Roomba can acquire is the linchpin for further product integration. By themselves, current smart home products can’t really discern all that much about your house. As Bloomberg states, a smart home, “only knows that your Philips Hue lightbulbs and connected television are in your sitting room because you’ve told it as much. It certainly doesn’t know where exactly the devices are within that room. The more it knows about a given space, the more tightly it can choreograph the way they interact with you.” Nothing creepy about that. With the 2018 acquisition of Ring home security cameras, Amazon now has an unparalleled ability to monitor your home. At best, it means Amazon will be able to finely tailor advertisements to each individual consumer. At its worst, this kind of data could provide interested parties – perhaps through third-party brokers – with invasive information about you. We have already seen how Amazon has made agreements with thousands of police departments across the country to share video data from Ring cameras and to enable monitoring of entire neighborhoods. Who knows what can be done with the information Roomba can provide about the interior of your home? A federal jury this week in San Francisco convicted Ahmad Abouammo, 44, who managed partnerships in the Middle East and Africa for Twitter, of six charges related to accusations that he spied on the company’s users for Saudi Arabia. During the two years that Abouammo worked for Twitter, he developed close relationships with advisors close to Saudi Arabia’s crown prince, Mohammed bin Salman. The deal? The jury found that Abouammo sold private information and data about dissident accounts to the Saudi government in exchange for bribes that included luxury watches and $300,000 in cash.
This case highlights just one way in which the political, financial, health, and personal information of Americans is at enormous risk of falling into the hands of foreign governments, as well as our own government. Abouammo, who worked at Twitter from 2013 to 2015, wasn’t arrested until 2019. Another former Twitter employee who was also charged in the scheme fled the country before he could be arrested. This human intelligence approach to spying, however, may be dwarfed by the scale of corporate infiltration and commercial surveillance by governments. China leads the pack in deploying the most sophisticated methods to infiltrate U.S. companies, capabilities recently described by FBI Director Christopher Wray: "China often disguises its hand in order to obtain influence and access where companies don’t suspect it. Outside of China, their government uses elaborate shell games to disguise its efforts from foreign companies and from government investment-screening programs like CFIUS, America’s Committee on Foreign Investment in the U.S.” Foreign infiltration operations are not the only way in which Americans’ personal data is hemorrhaging. Even if the U.S. government and companies could effectively catch spies and corporate infiltrators, countries around the globe might legally circumvent the FBI by simply buying our data from data brokers. “The present risks of our citizens’ data being sold to foreign governments are grossly underappreciated,” wrote Klon Kitchen and Bill Drexel at the American Enterprise Institute. As PPSA has previously reported, data brokers gather a trove of highly personal data about you and sell it to interested parties. Even if the U.S. can enact effective reforms to stop foreign infiltration, governments, including our own, can simply purchase our data. It is more important than ever that Congress and American businesses tackle the many threats to data privacy. As Congress debates a privacy bill, the scope of foreign government purchases of our information – perhaps through shell companies – should be the subject of deep inquiry. Addressing this vulnerability will require a lot of study by the relevant Congressional committees and social media companies to ensure that any proposed solution works without unintended consequences. In the meantime, there is one gap that can be closed immediately – the warrantless access of Americans’ personal information by U.S. law enforcement and intelligence agencies, in defiance of the Constitution’s Fourth Amendment. The House Intelligence Committee recently held an open hearing on commercial cyber surveillance, also known as “mercenary spyware.”
The hearing focused on new threats posed specifically by privately made, foreign-developed spyware that are bringing capabilities long associated with top-tier nation states to smaller countries and the private sector. PPSA has previously reported on one such foreign spyware, in particular the spreading “zero-click” Israeli-developed Pegasus. Pegasus can transmit itself seamlessly into a smartphone without a single click or action from the victim. From there, it can watch you through your camera, listen to you through your microphone, copy your messages, record your calls, extract all your images, and follow your movements. In just a few years, Pegasus has been acquired by dozens of countries and entities, from Saudi Arabia to Mexican cartels, and has already been used to deadly effect against dissidents and journalists. It represents the most sophisticated and widely available form of spyware yet developed. Among the hearing’s testimonials was John Scott-Railton, a senior researcher at The Citizen Lab of the University of Toronto's Munk School of Global Affairs & Public Policy. His testimony provided a stark picture to Congress:
Railton testified (see the 18:50 mark), “Your phone can be on your bedside table at two in the morning. One minute, your phone is clean. The next minute, the data is silently streaming to an adversary a continent away. You see nothing.” He added it was “capabilities available only to a handful of nation-states … It is too late,” he said, “to put the tech back into the bottle, and so we must take strong action now…” Another witness was Carine Kanimba, an American citizen born in Rwanda. Her testimony (29:05) details the story of her stepfather, Paul Rusesabagina, portrayed by Don Cheadle in Hotel Rwanda. Rusesabagina was the manager of the Hôtel des Mille Collines in Kigali during the Rwandan genocide. He used the hotel to save more than a thousand refugees. Later, he and his family fled to the United States. Rusesabagina became a public speaker and was critical of the human rights violations of the Rwandan government and of the Rwandan President Paul Kagame. In August 2020, Kanimba’s stepfather was surveilled in the United States by the Rwandan government and lured from the family home in Texas. Rusesabagina was kidnapped in Dubai, transferred to Kigali, tortured, tried, and sentenced to 25 years in prison. Kanimba became a vocal and effective activist about the abduction of her stepfather. In February 2021, Carine Kanimba was notified (33:11) by forensics experts that her smartphone had been infected by Pegasus. “I was mortified, and I am terrified,” she said. The forensics report showed “the spyware was triggered as I walked in with my mom into a meeting with the Belgian Minister of Foreign Affairs. It was active during the calls with the U.S. Presidential Envoy for Hostage Affairs team and the U.S. State department, as well as U.S. human rights groups.” Not only was Kanimba’s phone infected, but so was the phone of her cousin with whom she lives. “I am frightened by what the Rwandan government will do to me and my family next,” she said. “It keeps me awake that they knew everything I was doing. Where I was, who I was speaking with, my private thoughts and actions, at any moment they wanted. Unless there are consequences for countries and their enablers which abuse this technology, none of us are safe.” The threat by mercenary spyware companies and malware is too serious to ignore. “It has taken us too long to have this conversation,” concluded Railton. His testimony included several suggestions for Congress (22:15):
Video starts at Sen. Mike Lee's questioning of FBI Director Wray (1:02:00 mark).
At a Senate Judiciary Committee hearing yesterday, Sen. Mike Lee (R-UT) neatly summarized the FBI’s spotty observance of Section 702 of the Foreign Intelligence Surveillance Act (FISA), up for reauthorization next year, in his questioning of FBI Director Christopher Wray. Sen. Lee’s questions follow up on the revelation that the FBI used U.S. person information in FISA queries some 3.4 million times in a recent one-year period. Sen. Lee said: “As you know, Director Wray, Section 702 authorizes the collection of electronic communications. Not just the metadata but the content of the communications themselves, including communications of non-U.S. persons outside the United States. But, as you know, this inevitably leads to the incidental collection of communications that involve or include U.S. persons, including U.S. citizens.” The Utah senator reminded Director Wray that the 2018 reauthorization of Section 702 required the FBI to obtain an order from the Foreign Intelligence Surveillance Court to authorize querying the database for communications involving U.S. persons and citizens in criminal investigations not involving national security. Why then, Sen. Lee asked, did a recently released transparency report estimate that the FBI did not obtain a single order under section 702 from the Foreign Intelligence Surveillance Court in 2021? The FBI itself, after all, identified at least four instances in which the electronic communications of U.S. persons “were unlawfully searched without the required order from the Court?” Sen. Lee asked: “Can you tell me how you found those four instances and how you can be certain that there are not more than four instances in which someone did a backdoor search of U.S. persons’ communications?” The FBI Director said he could not recall the “various oversight mechanisms we have.” He noted that the FBI set up a new office of internal audit focused on FISA compliance. Sen. Mike Lee replied that he understood these authorities are needed to protect the American people. “But when it comes to American citizens, they have a reasonable expectation of privacy. When you have that much ability to collect that much information, record that many conversations of unsuspecting, law-abiding American citizens, there really do have to be procedures in place to make sure that there is probable cause and a probable cause-based warrant in order to search those, because that really is just a backdoor search and a potential end run around the Fourth Amendment.” Senator Lee expressed skepticism that the four known surveillances of Americans did not require a FISC order. And said he would hold Director Wray to his promise to provide more information. If you are ever a witness before a Congressional committee, the trick to surviving a contentious hearing is to run out the clock with smooth talking. Each committee member only has five minutes to ask questions. An expert witness will often respond to a precise and penetrating question by taking up minutes with a Wikipedia-level recitation of a law or process, wrapped within pleasing-sounding banalities and blandishments.
Even within time constrictions in facing a polished witness, Rep. Zoe Lofgren (D-CA), long-time watcher of the watchers, managed to challenge the Department of Justice on Section 702 of the Foreign Intelligence Surveillance Act (FISA) in the recent House Judiciary Committee hearing. Rep. Lofgren refused to be brushed off (29 minutes mark) by the Department of Justice’s top national security official, Assistant Attorney General Matthew G. Olsen, concerning the FBI’s use of Section 702 information – collected to catch foreign terrorists and spies – against Americans. Rep. Lofgren began by noting that FISA Court Judge James E. Boasberg had found that the FBI improperly searched Americans’ personal information collected without a warrant. Some of these were run-of-the-mill criminal investigations involving healthcare fraud, bribery, and other purported crimes unrelated to national security. Rep. Lofgren added that in Dec. 2020 to Nov. 2021, the FBI searched the personal identifiers of known Americans in 702 data some 3.4 million times. This was triple the number from the previous year. As PPSA has reported, that amounts to more than 9,300 searches by the personal identifiers of Americans every day. Rep. Lofgren noted that when Olsen went before the Senate Intelligence Committee for his confirmation, he pledged that “restoring and maintaining trust in the FISA process was a critical priority.” She asked him what he has done since to prevent warrantless, improper, backdoor searches of Americans’ data conducted under Section 702? After taking time to give a topline description of the law, Olsen admitted that the “issues you cite are ones of concern” and promised to improve FBI compliance with training and by upgrading FBI computer systems. “We are looking forward to improving the compliance record of the Department of Justice and the FBI in regard to Section 702,” Olsen said, “and I can assure you it is a priority.” Rep. Lofgren had a sharp reply. “We have had reassurances over the years and yet the performance continues to be poor, and it has been poor under both Republican and Democratic Administrations,” she said. “We have considered imposing a warrant requirement for queries of known Americans … probably a necessity unless we can get some further, definitive control of the warrantless search of Americans in the 702 database.” Rep. Lofgren added that using Section 702 to conduct warrantless searches on Americans is “improper and yet it continues.” Olsen replied that Section 702 permits the creation of a database of non-U.S. persons overseas, and that when the FBI searches, it does so to simply find “connections,” not to target Americans. Rep. Lofgren’s retort was sharp: “That is contrary to the report that we got from ODNI and from the FISA Court.” As Section 702 faces reauthorization next year, civil libertarians should continue to press Rep. Lofgren’s questions and urge Congress to consider an explicit warrant requirement when queries target Americans. |
Categories
All
|

















 RSS Feed
RSS Feed